Tenable Cloud Security 2.1 Release Notes (2021-12-21)
New Features
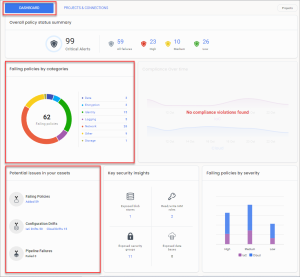
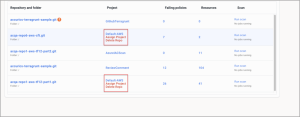
The dashboard has the following enhancements:
-
Dashboard interface - The dashboard interface has been improved to better display trends for policies, issues, security insights, resources, service tickets, and PRs.
-
Failing policies by categories - This is a new widget that displays policies that failed, categorized by the reason the policy failed.
-
Potential issues in your assets - This is a new widget that displays failing policies, configuration drifts, and pipeline failures in your assets.
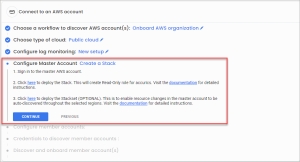
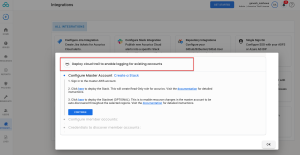
The AWS organization onboarding is enhanced with the following features:
-
Ensure that the resources with the same name do not exist.
-
Added a warning not to change the account number.
-
Added a note that the AccuricsReadOnlyRole should have an external ID listed in the output of the stack deployment.
-
The Configure Master Account setting is now optional if you do not want to monitor the master account.
-
The URLs have been updated to point to create stack/stacksets instead of list stack/stacksets.
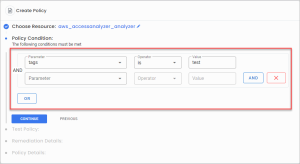
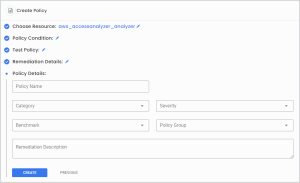
There is a new policy editor for custom policies with the following features:
-
Easier user interface - The process of creating the policy follows a step-by-step workflow similar to creating a project or connection.
-
Building policies - You can build policies against any cloud resource/schema supported by the IaC providers.
-
Query builder - There is a simple visual query builder for setting conditions for the policy. This query builder supports AND and OR expressions. The query builder options are dynamic and based on the resource’s schema.
-
Test policies - You can test policies against projects if you have user access.
-
Policy-based operations - You can perform all the policy-based operations via the API
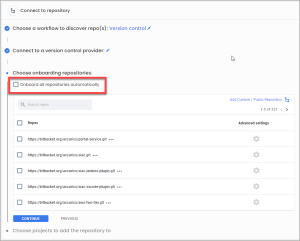
The role-based access control (RBAC) for default projects has been updated with the following:
-
If a user onboards a repository in pipeline mode, then the user is assigned a viewer role on the default-AWS project.
-
If a user onboards using a config file for a specific project, then the user is assigned a viewer role on that project.
Known Issues
-
Scanning Cloudformation code from the command line raises a 413 error.
-
Some policies are missing the corresponding benchmarks.
-
When you ignore all resource violations under a policy, all the violations should be ignored and moved to ignored violations. However, some violations remain in the unignored section.