Tenable Cloud Security 2.2 Release Notes (2022-01-06)
New Features
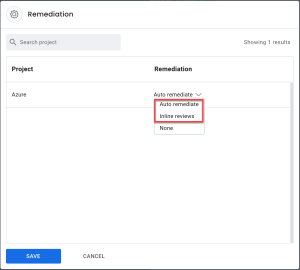
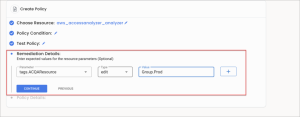
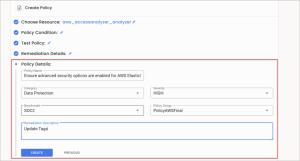
The following enhancements are added for creating and editing a policy:
-
Create remediation: You can add remediation (expected criteria) for policies during policy creation.
-
Compliance benchmarks: You can create a user-defined compliance benchmark and add the requisite policy to the created benchmark.
-
Selection of a custom policy group: While creating or editing a policy, you can select the requisite custom policy group.
-
Edit policies: After the policies are created, you can edit the policies as needed.
-
Search policies: The enabled Search option on the Edit Policy window allows you to search for and edit the requisite policy.
APIs are now provided for project repository, scan and pull requests for the pipeline. The Public API requires support for the following:
-
API interactions with the project object: Execute the following commands for the API interactions with the project object from within the pipeline:
-
GET /projects — Retrieves all the projects accessible by the user
-
POST /projects — Creates a new project
-
GET /projects/{projectId} – Retrieves the details of the project identified by the projectId
-
-
API – API interactions with the "repo" objects: Execute the following commands for the API interactions with repo objects from within pipelines, with the assumption of tfplan based scanning:
-
GET /repos — Returns all the repositories
-
POST /repos — Creates a repository
-
GET /repos/{repoId} — Returns the details of the repository identified by repoId
-
-
API – API interactions with the “scan” objects: Execute the following commands for the API interactions with scan objects from within pipelines:
-
GET /scan/{scanId} — Retrieves the status of scan
-
POST /repos/{repoId}/scan — Triggers the scanning of the IaC repository identified by repoId
-
-
API – API interactions with the “pull request” objects: Execute the following commands for the API interactions with pull request objects from within pipelines:
-
GET /pull_requests — Retrieves all the pull requests
-
POST /pull_requests — Creates a pull request
-
All the APIs have Role Based Access Control (RBAC). The administrator users have access to POST, and the read-only users have access only to GET.
You can scan and push Kubernetes cluster results from the CLI in pipeline mode. A Default-AWS / Default-AZURE / Default-GCP project is created, and the newly pushed cluster is assigned to the project.
You can also create a new project as the default project with the same provider type, and from the fly-out window, you can edit associated clusters. After running a subsequent scan via CLI, it is linked to both the default and the new project.
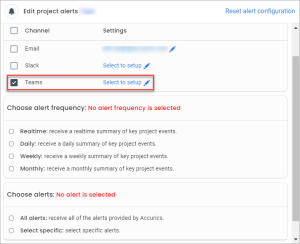
You can configure Microsoft Teams within the Project settings and set the alert service by configuring the channel through the webhook URL.
For the detail process of setting the alert, click Microsoft Teams.
-
Removed Terragrunt: Terragrunt is removed as a configurable option in the advanced settings for repositories. You can configure Terragrunt through CLI.
-
Spinners showing loading message: Spinners are added across various tabs on the dashboard to indicate the loading of data. It also displays a "Loading" message.
-
Renamed tab: On the dashboard, the Compliance Violations Over time tab is renamed as Compliance Over Time.
-
KPI removed: The KPIs that were present under the Projects & Connections tab are removed.
-
Default sorting capability: You can use the default sorting capability across grids.
Known Issues
-
When scanning multiple repositories simultaneously, the Web console shows fewer resources/violations, as compared to the GitLab repository pipeline results.
-
When a project is deleted, the context history associated with the project gets deleted.
-
After a policy is created with requisite policy condition and is associated with a policy group and the corresponding project, the scan fails to detect the policy failure. On changing the policies on a project that has a cloud account, cloud scan must be manually initiated to re-evaluate the results.
-
Dashboard widgets render no data on the dashboard when updates are made to a lot of policies. To fix this issue, perform an IaC or Cloud scan in any of the existing projects.
-
After performing a Kubernetes (K8s) cloud scan, kubernetes_container_process and kubernetes_namespace resource types are not assigned a cluster_uid.