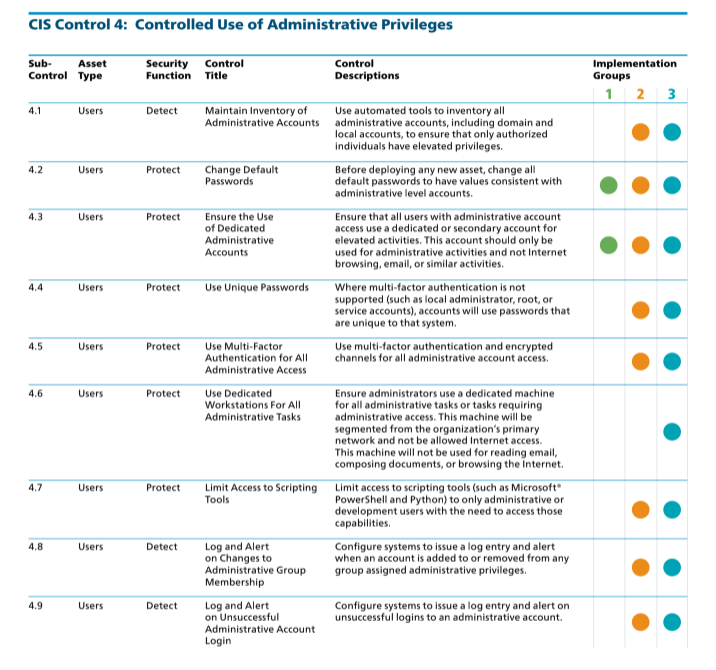
CIS Control 4: Controlled Use of Administrative Privileges
The focus of this control is to ensure that all users with administrative level access use a dedicated or secondary account for any elevated activity. This administrator account should not be used for any other purpose, and should not be used for email, web-browsing, or similar activity.
The CIS states this Control is critical:
“The misuse of administrative privileges is a primary method for attackers to spread inside a target enterprise. Two very common attacker techniques take advantage of uncontrolled administrative privileges. In the first, a workstation user running as a privileged user is fooled into opening a malicious email attachment, downloading and opening a file from a malicious website, or simply surfing to a website hosting attacker content that can automatically exploit browsers. The file or exploit contains executable code that runs on the victim’s machine either automatically or by tricking the user into executing the attacker’s content. If the victim user’s account has administrative privileges, the attacker can take over the victim’s machine completely and install keystroke loggers, sniffers, and remote control software to find administrative passwords and other sensitive data. Similar attacks occur with email. An administrator inadvertently opens an email that contains an infected attachment and this is used to obtain a pivot point within the network that is used to attack other systems.
The second common technique used by attackers is elevation of privileges by guessing or cracking a password for an administrative user to gain access to a target machine. If administrative privileges are loosely and widely distributed, or identical to passwords used on less critical systems, the attacker has a much easier time gaining full control of systems, because there are many more accounts that can act as avenues for the attacker to compromise administrative privileges.”
The journey of implementing the CIS Controls continues with controlled use of administrative privileges. Organizations are directed to verify that users with high-privileged accounts are not using privileged accounts for non-administrative activities such as web surfing and email. The two specific sub-controls that are part of Implementation Group 1 (IG1) are:
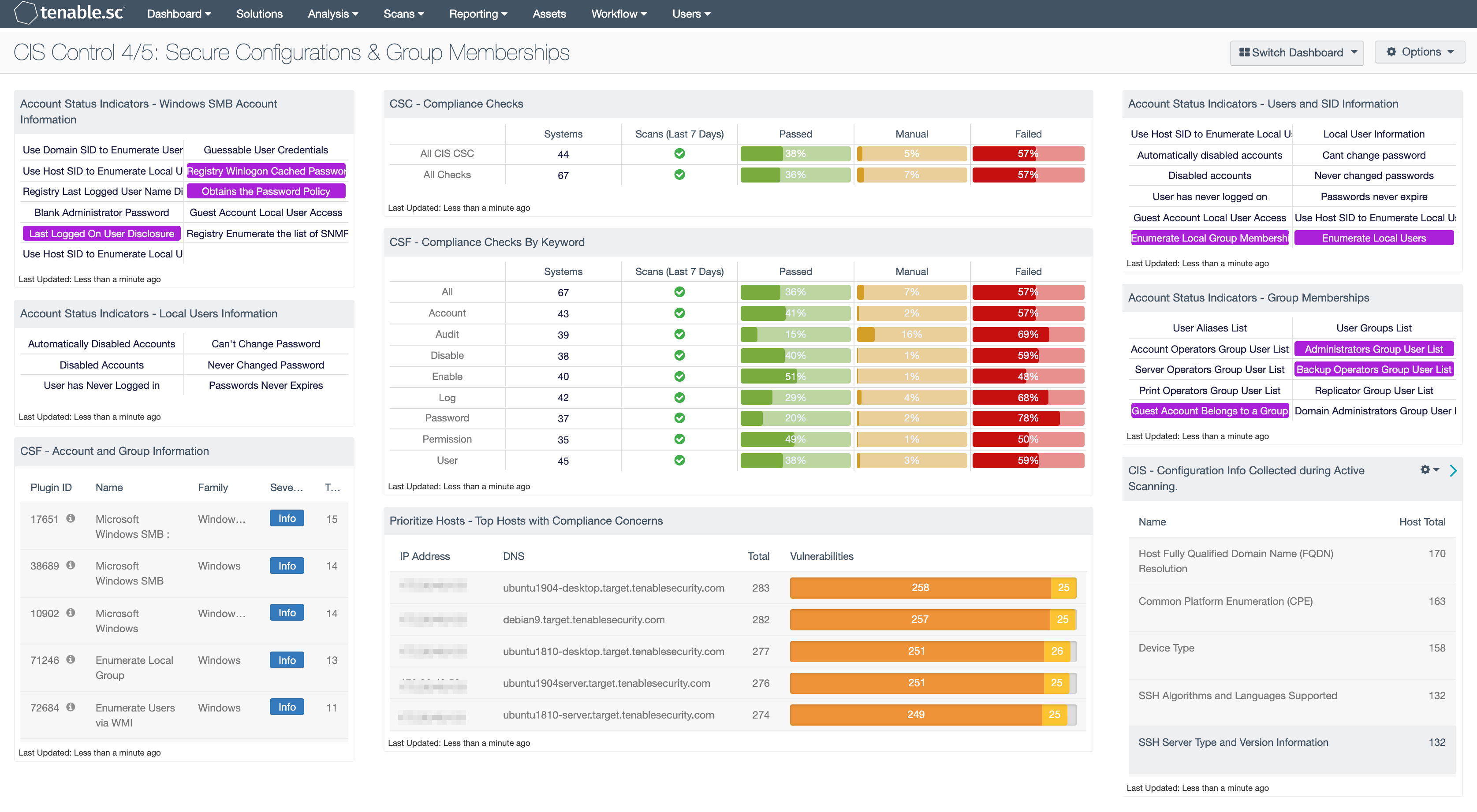
For CIS Control 4, Tenable products allow security operations teams to use Tenable Security Center Continuous View to analyze group membership in local and domain groups. In addition to plugins that help monitor for group membership, there are also plugins that track the processes, services, and other related indicators of elevated privileges.
A vital step in vulnerability management is assessing the configuration of systems within the network. The CIS Control 4/5 Secure Configurations and Group Memberships Dashboard provides useful information to assist organizations with this control.
For more information about the CIS Control 3 dashboard, see CIS Control 4/5: Secure Configurations & Group Memberships.
NIST also provides helpful information directly related to this CIS Control under the NIST Digital Identity Guidelines.
The CAS provides guidance on how to assess the organization's progress in this journey. This guide illustrates how the CISO can effectively measure progress through the vulnerability management program. Shown below are the CIS Control 4 IG levels and requirements: