Access Recast Rules from Settings
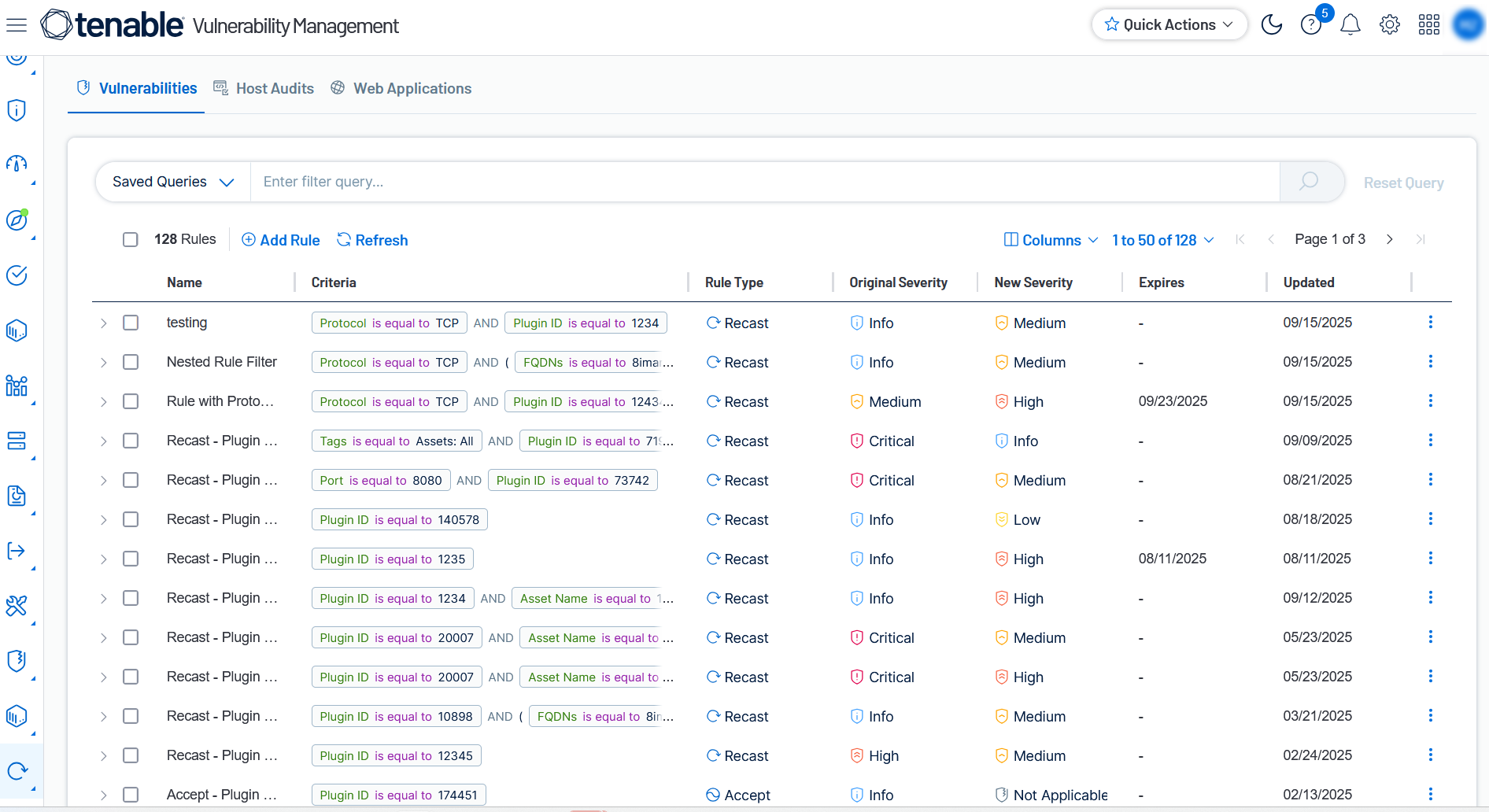
Customizing your risk management framework allows you to align scan findings with your organization's specific security posture and policies.Tenable Vulnerability Management provides three primary tools for this purpose: Recast rules adjust the CVSS-based severity of vulnerabilities and web application findings; Change Result rules manually override host audit statuses to reflect specific compliance states; and Accept rules formally acknowledge and hide risks that do not require active remediation. These rules ensure that dashboards and reports accurately reflect the current risk profile of your environment.
For more information on recast, change result and accept rules, see Recast .
To access the Recast page via Settings:
-
In the left navigation, click
 Settings.
Settings.The Settings page appears.
-
Click the
 Recast tile.
Recast tile.The Recast page appears.
Here, you can view information about your recast rules.
To add recast, accept, or change result rules, see Add Recast, Change Result, and Accept Rules.
To view findings impacted by any rule type, see About Recast Rules, About Change Result Rules, and About Accept Rules.
For more information on editing, disabling or deleting rules, see Manage Recast Rules.