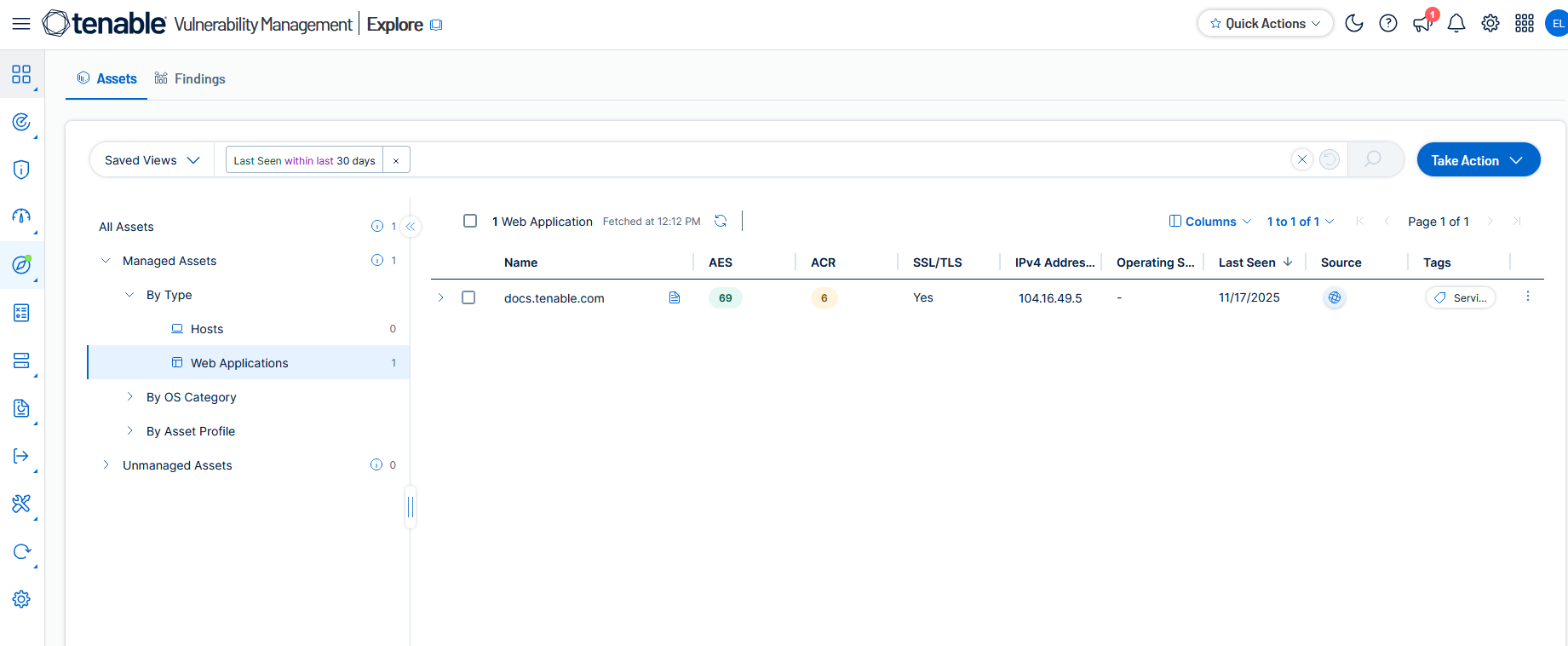
Assets
Assets are entities of value on your network that can be exploited. They include laptops, desktops, servers, routers, mobile phones, virtual machines, software containers, and cloud instances. Use the Assets page to view all the assets in your environment that Tenable Vulnerability Management has a record for. These are broken down into categories such as hosts, web applications, and network devices.
The following topics explain how to view and export lists of assets, build custom queries with filters, add assets to scans, and more.