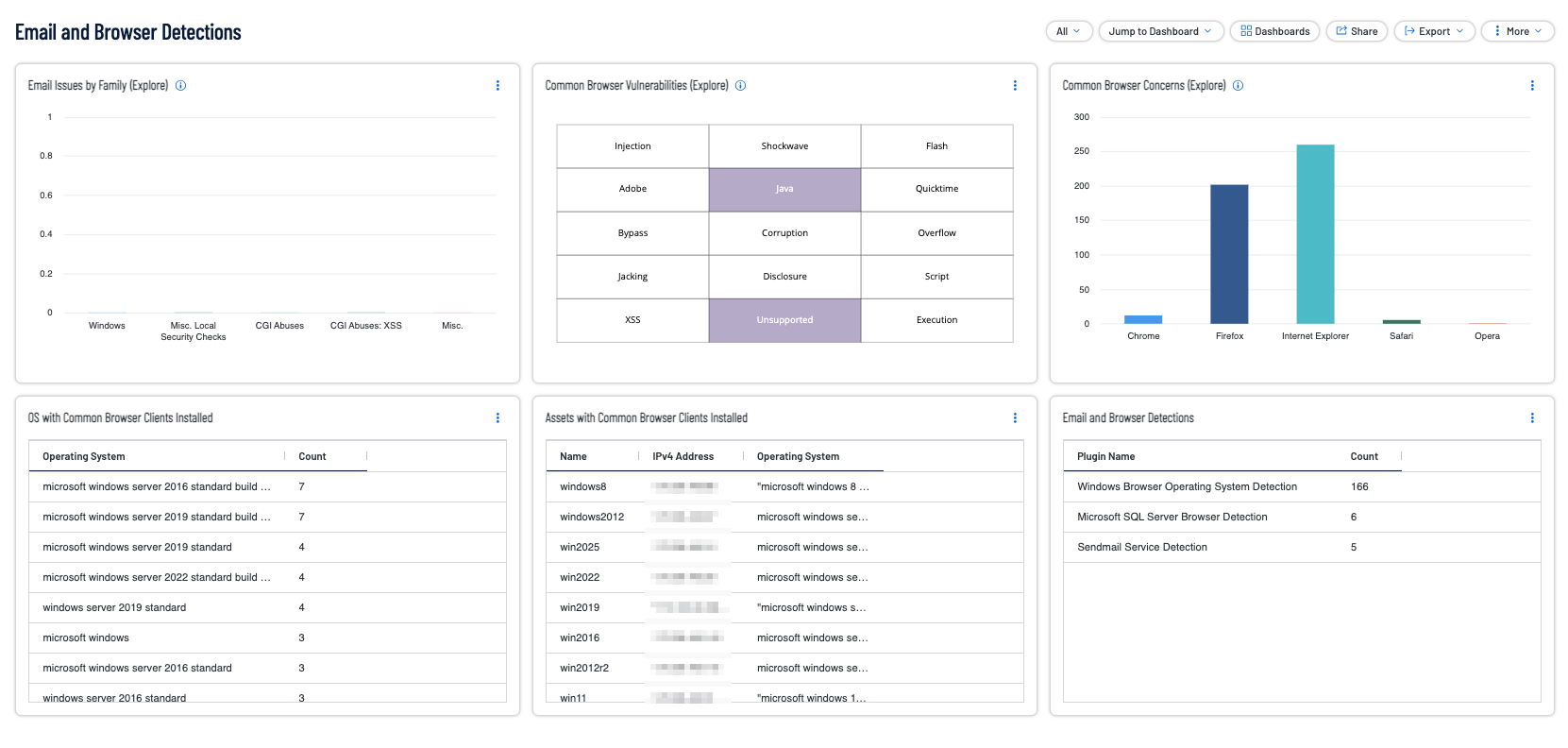
Ensure the Use of Only Fully Supported Email and Browser Clients
Tenable products allow security operation teams to use Tenable One to analyze endpoint browser and email client configurations. Using a variety of active and passive plugins paired with Tenable Vulnerability Management, the organization can verify that established configuration policies are followed. Tenable provides several solutions for organizations to better understand vulnerability management. As an example, the Tenable Network Monitor can passively detect and enumerate web browsers that are being utilized, as well as any potential vulnerabilities present in the versions detected. Active, credentialed, scanning by Tenable Nessus can provide detailed information on web browsers that are installed via the same methods of software enumeration described in the relevant CIS Controls. Analysts can easily produce tables and matrices utilizing this information, for a variety of browser clients such as Chrome, Firefox, Internet Explorer, Safari, and more, which are part of the Email and Browser Detections Dashboard for Tenable Vulnerability Management, as shown in the following image: