Identifying Exposure
Tenable Identity Exposure provides various methods to access the information collected through the Indicators of Exposure (IoE) and Indicators of Attack (IoA) panes. Tenable Vulnerability Management provides the ability to use the Explore Findings through the use of dashboards and reports.
Identification
The first step in taking control of the organization’s Identity Management is to enumerate every user account in the environment and determine the level of access the account is granted. All user accounts must be uniquely identified and assigned to particular entities, such as users and applications.
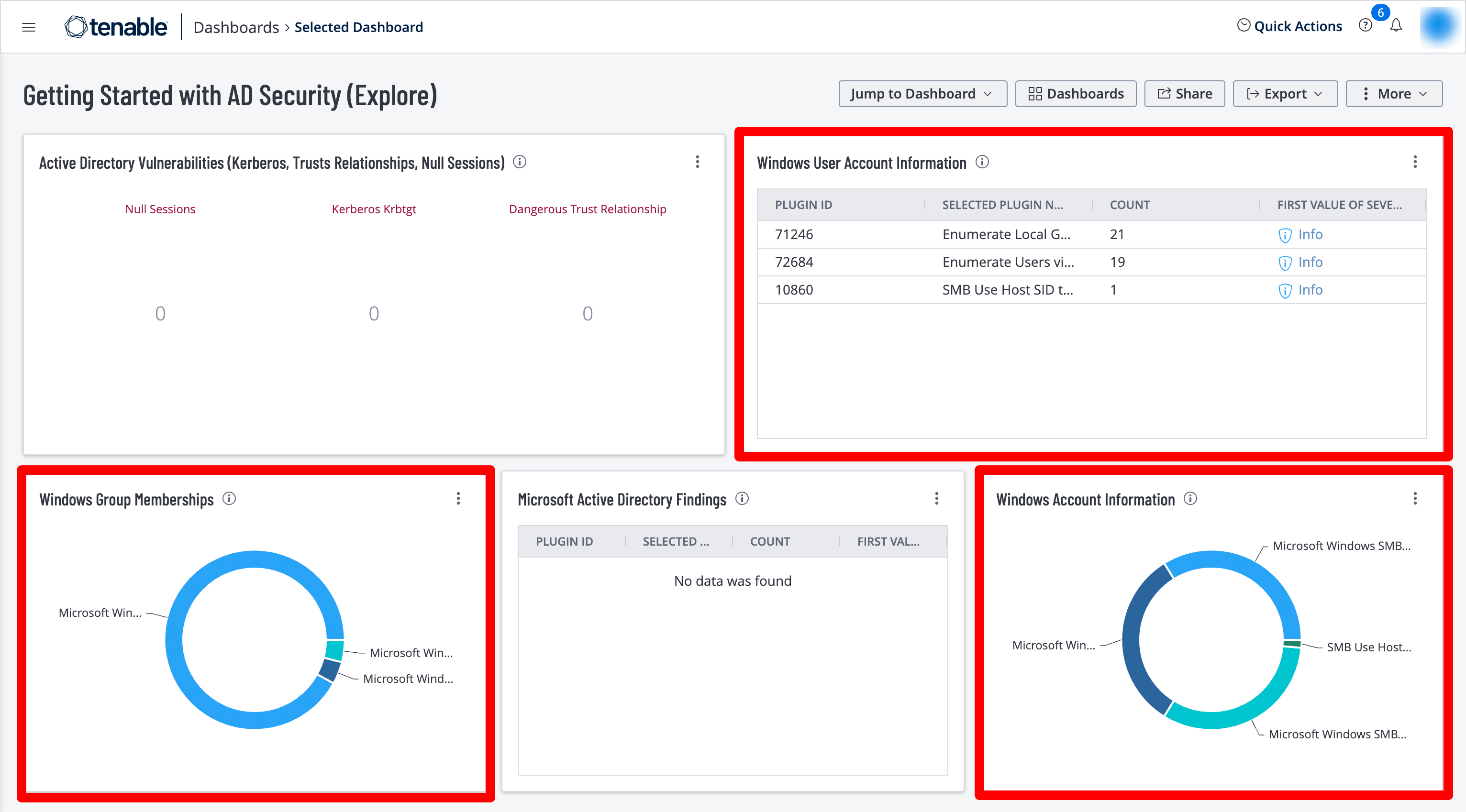
The Getting Started with AD Security dashboard in Tenable Vulnerability Management contains the following widgets to enumerate user accounts:
Windows User Account Information – This widget displays counts for user accounts and security identifiers (SID). Plugins report on potential user account vulnerabilities such as disabled accounts, accounts that have never logged in, accounts with passwords that have never changed, and more.
Windows Group Memberships – This widget displays information for Windows default groups such as administrators, server operators, account operators, backup operators, print operators, and replicator groups.
Windows Account Information – This widget displays counts related to Microsoft Windows SMB plugins that focus on user account information. Plugins focus on vulnerabilities such as SMB blank administrator passwords, SMB password policies, guest accounts, cached passwords, and more.
Organizations can use the CSF - Account and Group Information widget located in the CIS Control 4/5: Secure Configurations & Group Memberships dashboard in Tenable Security Center, which leverages plugins that enumerate Windows account information.
Users and Groups
While Active Directory is typically used by most organizations, there are many other accounts for non-Windows platforms that must be identified. Tenable Nessus contains a number of plugins and plugin families that help organizations enumerate users and groups on the network. The Windows: User management plugin family contains nearly 30 plugins that enumerate Microsoft Windows users and groups. Other useful Nessus plugins for user and group enumeration include:
-
10894 Microsoft Windows Users Group List – This plugin uses the supplied credentials to retrieve the list of groups each user belongs to. Groups are stored for further checks.
-
126527 Microsoft Windows SAM user enumeration – This plugin enumerates domain users on the remote Windows system using Security Account Manager.
-
95928 Linux User List Enumeration – This plugin enumerates local users and groups on the remote host.
-
95929 macOS and Mac OS X User List Enumeration – This plugin extracts the member lists of ‘Admin’ and ‘Wheel’ groups on the remote host.
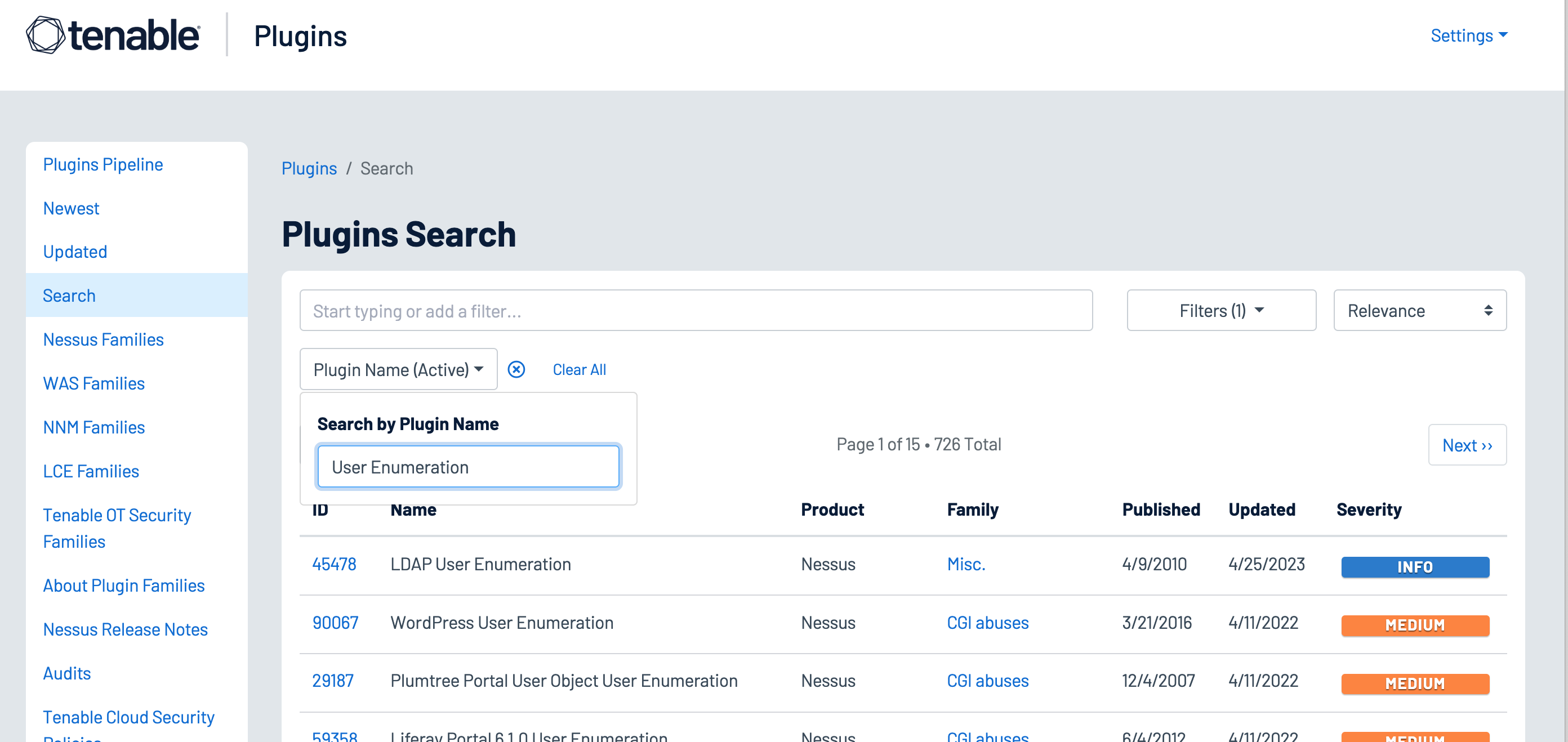
A number of other Nessus plugins that contain the key words “User Enumeration” in a plugin name search using the Plugin Name filter identify WordPress, VMware, LDAP, and other software applications that maintain user accounts, as shown in the following image:
Service and Default Accounts
Operating Systems and applications are often distributed with service and default accounts that are either not password-protected or have a default password that is well-known. Tenable Nessus and Tenable Identity Exposure help identify these accounts, enabling organizations to review and disable any unnecessary accounts to reduce the attack surface. Organizations can leverage the following Nessus plugins to enumerate service and default accounts:
-
Plugin Family: Default Unix Accounts – This plugin family contains over 170 Nessus plugins that check for the existence of default accounts/passwords on a number of devices. In addition, there are many plugins that check for simple passwords such as “0000”, “1234”, and more commonly identified password combinations for “root” or administrator accounts.
-
171959 Windows Enumerate Accounts – This plugin enumerates all Windows Accounts
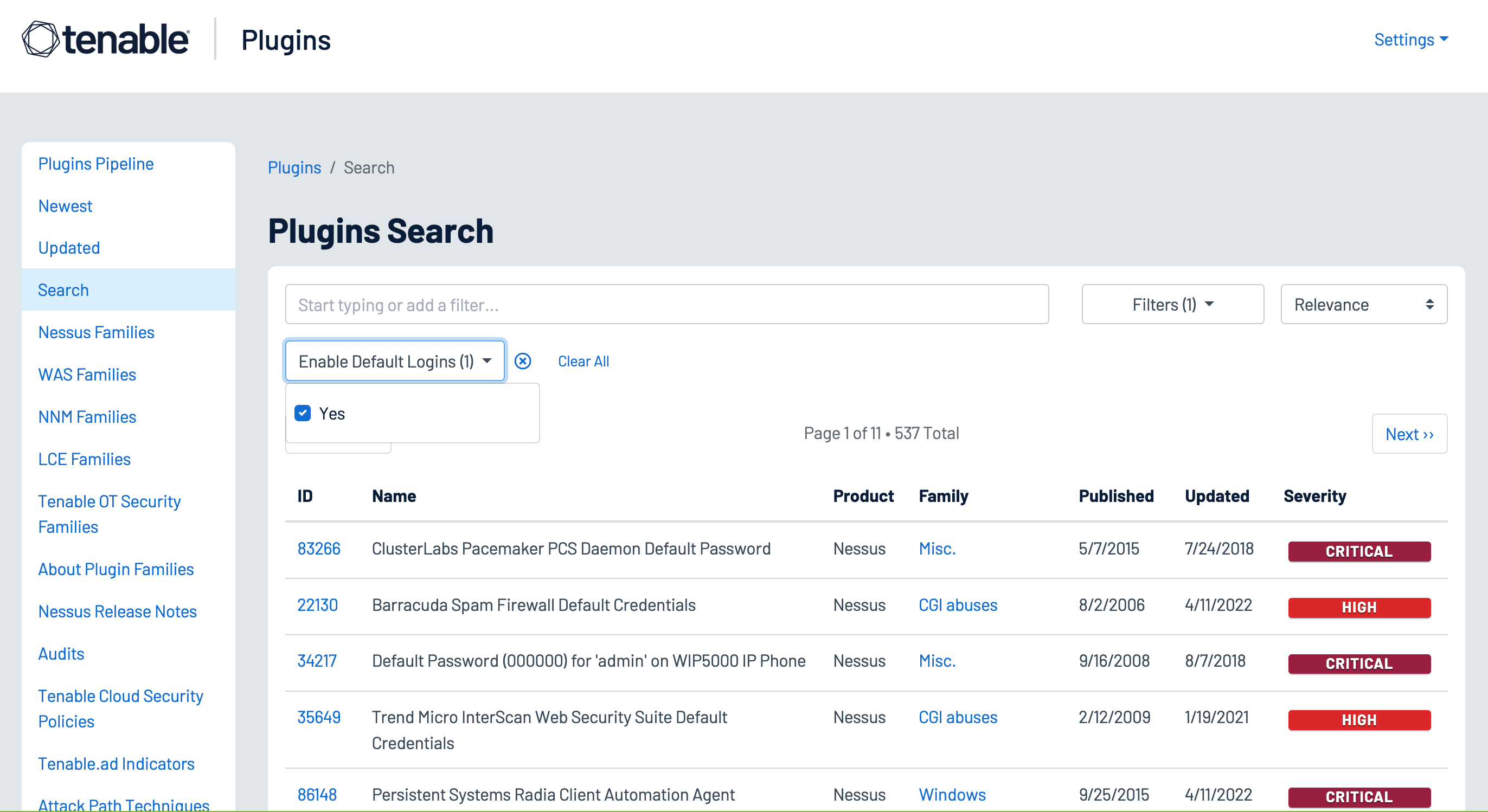
Several hundred plugins can be identified by searching for “Default Account” from the Nessus Plugins Search page using the Enable Default Logins filter. Nessus default account plugins are available for Databases, Web Servers, SCADA devices, Unix/Linux devices, Cisco devices and more. Many of the plugins are associated with the Default Unix Account Nessus family, however, many are in other families as well.
In addition, Tenable Identity Exposure provides the ability to determine if a default administrator account was recently used in the environment, as shown in the image below:
User Access Controls
Strong authentication mechanisms help validate that accounts are being used by the authorized user to read, create, modify, or delete data in accordance with business needs. The Center for Internet Security (CIS) provides benchmarks for a large number Operating System platforms and applications. Tenable Research writes audit files for these benchmarks to help organizations quickly determine their alignment with the CIS recommendations. The benchmarks include guidance on access controls for both non-privileged and privileged accounts.
User Accounts
Non-privileged user accounts require strong access controls to prevent attackers from gaining local access to the network. Attackers often target user accounts to exploit weaknesses in the local network and escalate privileges. Security teams can use the Tenable Audits Search Page to find audit files for their Operating System platforms, which check for common compliance requirements such as “Lock Workstations after Inactivity” and other issues.
Active Directory accounts can be configured to escape global password renewal policies. Accounts set up in this manner can be used indefinitely without ever changing their password. Tenable recommends reviewing user and administrator accounts to ensure they are not configured to have this attribute.
The following Indicators of Exposure (IoE) in Tenable Identity Exposure can be used to identify issues with user accounts in an organization’s Active Directory environment:
-
Accounts with Never Expiring Passwords
-
Application of Weak Password Policies on Users
-
Dangerous Kerberos Delegation
-
Account that Might Have an Empty Password
-
AdminCount Attribute Set on Standard Users
-
User Account Using Old Password
-
Kerberos Configuration on User Account
Privileged Accounts
Most compliance standards and frameworks require privileged users to have a non-privileged account for standard user activities, such as web browsing or reading emails. Tenable Nessus and Tenable Identity Exposure provide the tools to identify settings for root and admin accounts.
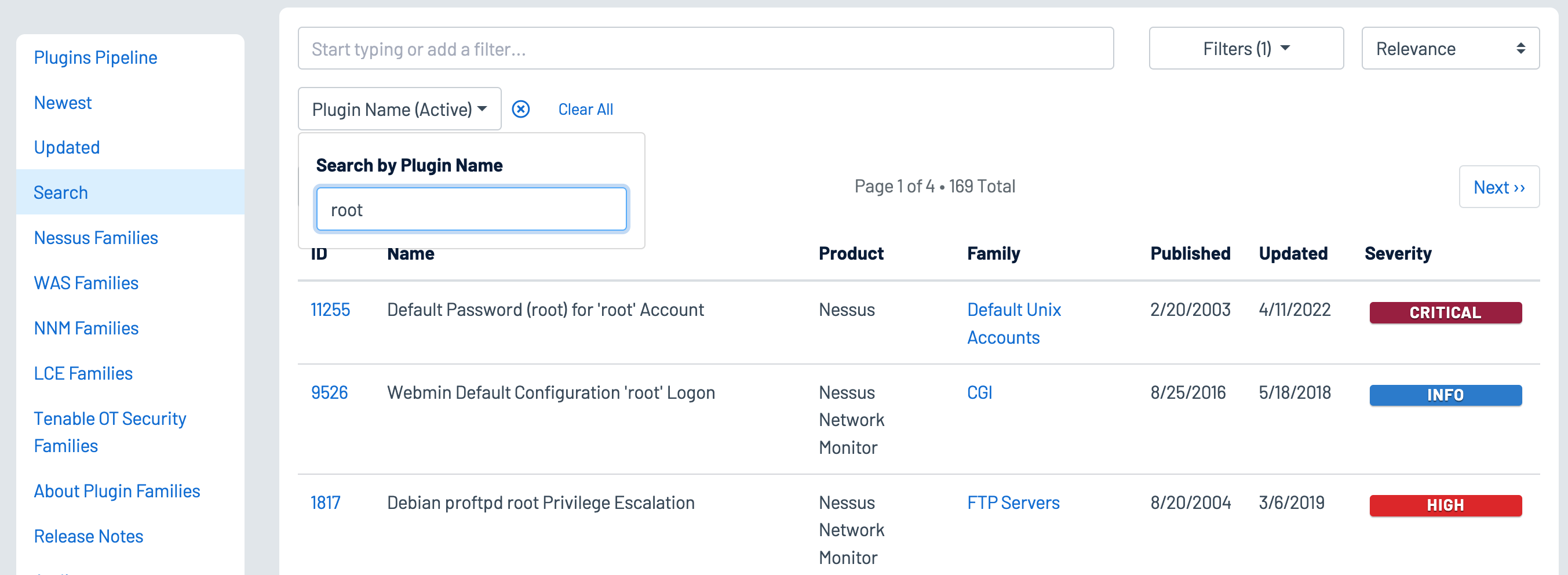
Using the Plugin Name filter on the Plugins Search page enables analysts to search for plugins with terms that identify privileged accounts such as “root,” “admin,” or “privileged,” as shown below:
The following Indicators of Exposure (IoE) in Tenable Identity Exposure can be used to identify Active Directory settings for privileged accounts:
-
Mapped Certificates on Accounts
-
Ensure SDProp Consistency
-
Native Administrative Group Members
-
Privileged Accounts Running Kerberos Services
-
Potential Clear-Text Password
-
Protected Users Group not Used
-
Logon Restrictions for Privileged Users
-
Local Administrative Account Overview Management
Dormant Accounts
User accounts that have not been accessed in more than a year provide an opportunity for attackers to leverage compromised credentials and perform brute-force attacks. Nessus plugins 10915 or 10899 Microsoft Windows - Local Users Information: User Has Never Logged In displays a list of Windows accounts where the user has never logged in. The Sleeping Accounts Indicator of Exposure in Tenable Identity Exposure detects accounts that have not been accessed in over a year.