Grouping Assets
Grouping assets by common functions and features, such as Operating System, platform, or business function facilitates vulnerability scanning and remediation by ensuring that scans are configured to probe for common weaknesses in the platform or application. Systems may be classified in multiple asset lists. For example, a Linux web server on the DMZ may be listed under “Linux Systems,” “Web Servers,” and “DMZ Systems.” This classification ensures that scans are targeted appropriately. Create asset lists that logically group assets, such as:
- Critical business servers
- Critical infrastructure devices
- Managed servers
- User / Desktop
- Off-site (VPN, Managed)
- Production servers
- Development servers
- Test systems
Maintaining a software inventory provides visibility into assets that align with specific software categories. This enables tracking assets with authorized, unauthorized, or unsupported software. Assets can be grouped in Tenable Vulnerability Management using Tags and in Tenable Security Center using Dynamic Assets.
Grouping Assets in Tenable Security Center
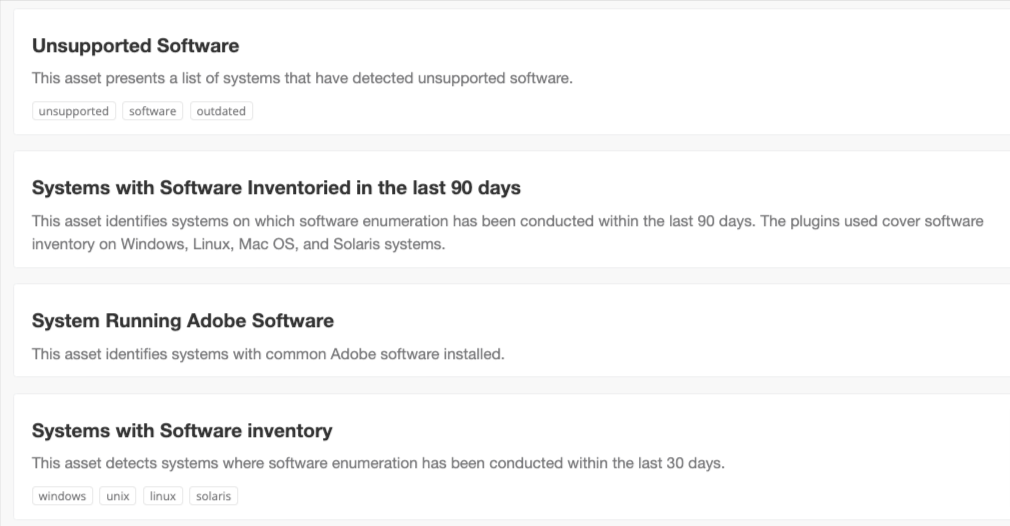
There are hundreds of built-in Asset templates in Tenable Security Center. A search for the word “software” displays a few of the asset templates, as shown below:
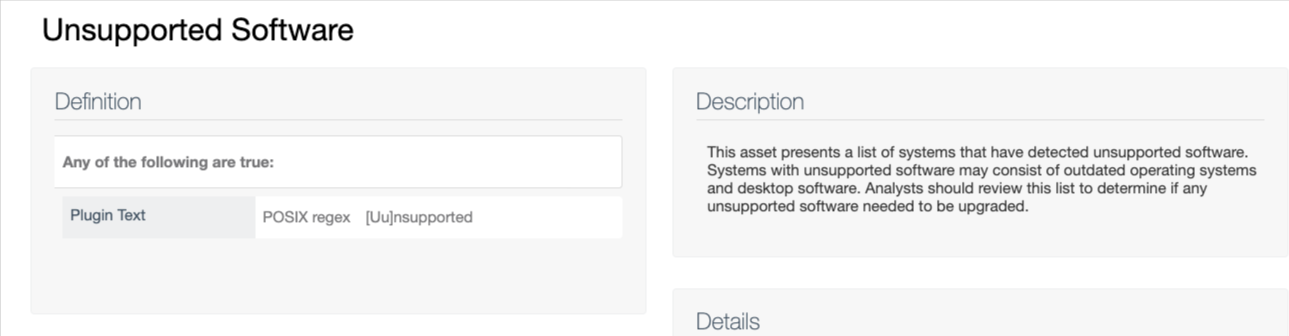
The Unsupported Software Asset template in Tenable Security Center uses a POSIX regex filter for Plugin Text (also known as vulnerability text or plugin output).
Custom Dynamic Assets can be created in Tenable Security Center using the filters in the list below. A good example is to use Plugin Text contains cpe:/a:oracle:jre where plugin ID is 45590.
Grouping Assets in Tenable Vulnerability Management
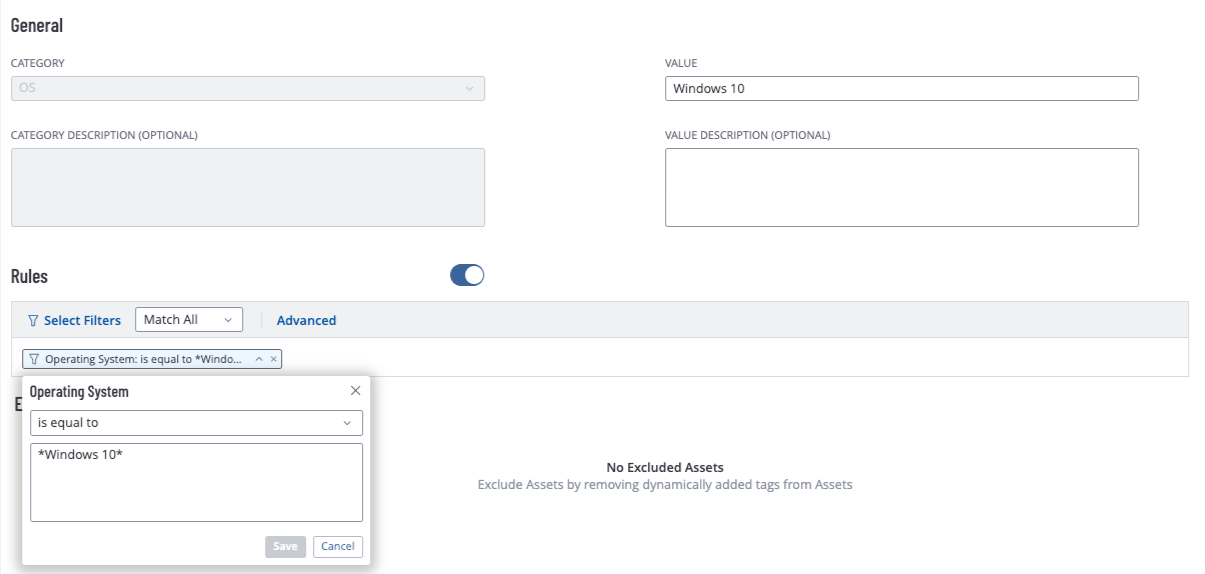
Assets can be grouped using Tags in Tenable Vulnerability Management. Dynamic tags are created using many of the filters that are available in Tenable Vulnerability Management. The following example displays the configuration for a tag that groups assets with a Windows 10 Operating System.
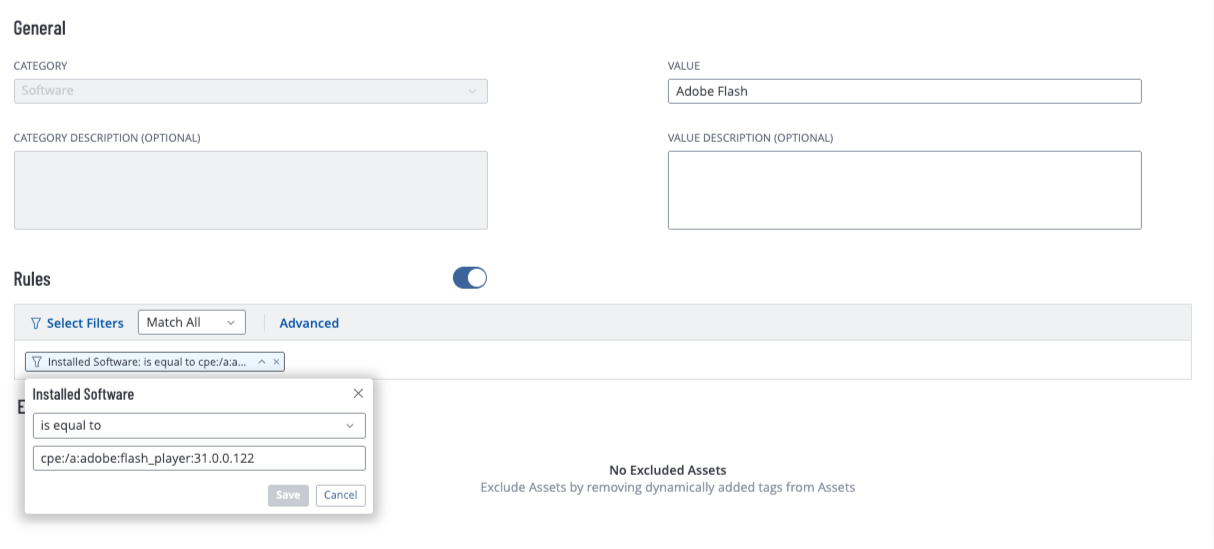
The CPE value can also be used to group assets by software installed, as shown in the following image for Adobe Flash.