Configure QRadar with OT Security
Overview
OT Security enables operational engineers and cybersecurity personnel to gain visibility into, and control over, Industrial Control System (ICS) networks. Through its policies and alerts mechanism, OT Security generates real-time alerts that are accurate, actionable, and customized for each network and its unique needs. OT Security detects unauthorized changes made to industrial processes in ICS networks. It can produce various alerts on changes in the configuration of controllers (PLC, DCS, IED), details, communications, and alert on a range of network attack vectors that may threaten industrial processes. OT Security also actively verifies the controllers’ configuration and alerts on changes made to them. OT Security reports these alerts to QRadar via Syslog. For each individual policy, you can decide whether an alert should be sent to QRadar via Syslog; this offers them maximum control over which information is being sent.
When configuring QRadar with OT Security you must create a log source through the Log Source Management application for ingesting data from the Tenable platform.
To configure the OT Security App For QRadar v4.3.0:
-
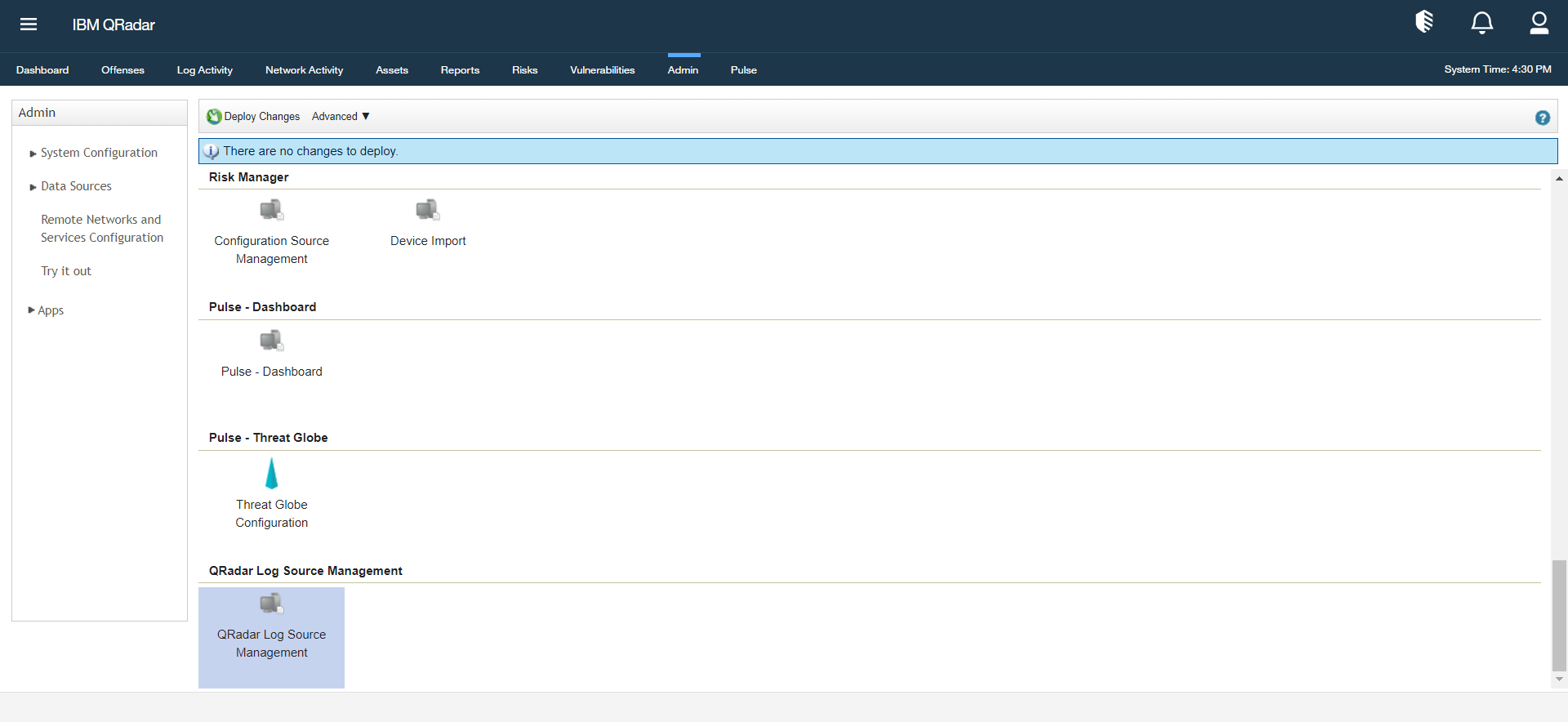
Go to the QRadar Log Source Management application in the Admin panel.
The Log Source Management page appears.
-
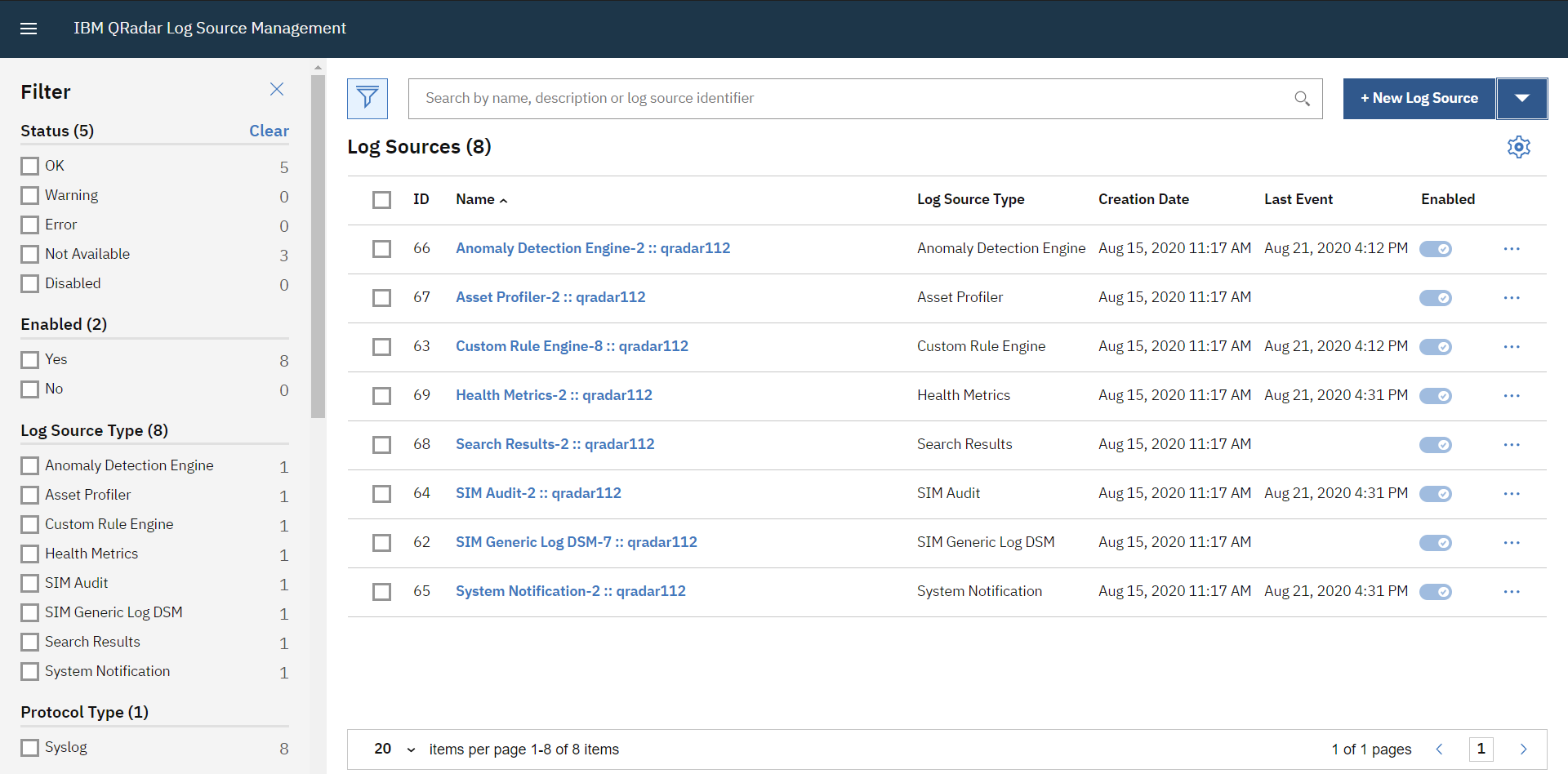
Click + New Log Source in the upper-right.
The Log Source Management page appears.
-
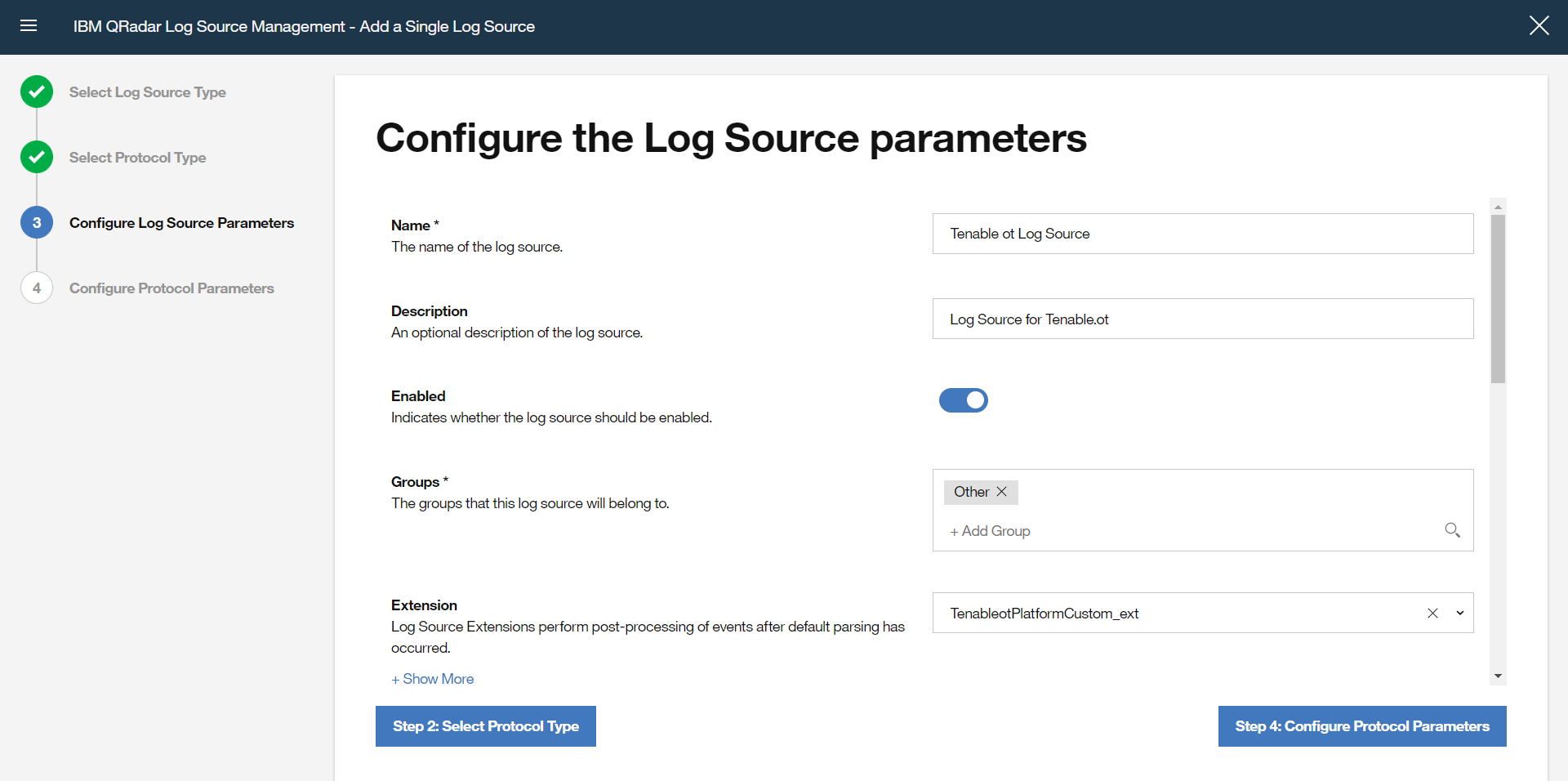
Select Tenable.ot Platform as the Log Source type.
-
Select Syslog as the protocol type.
-
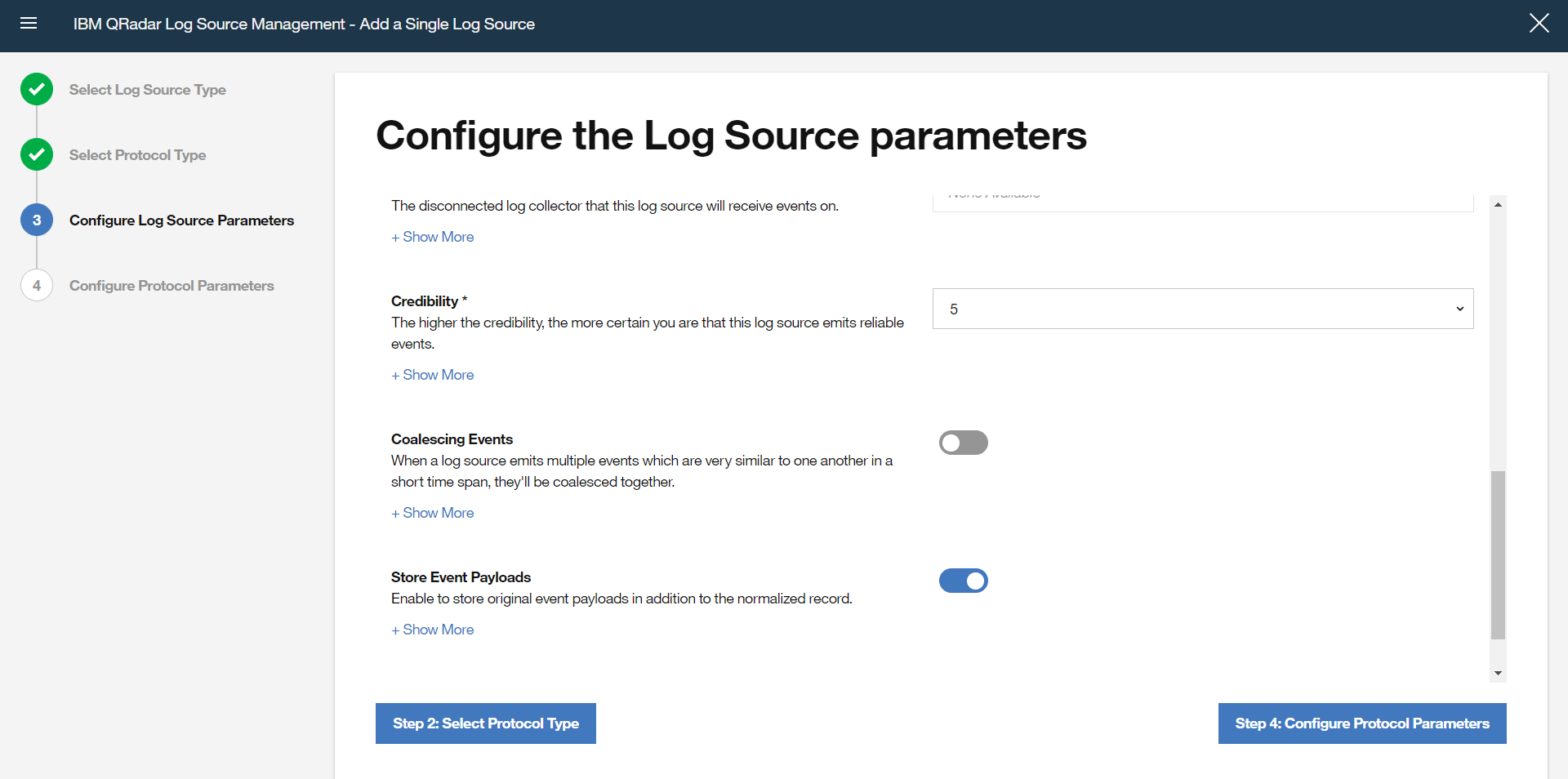
In the Configure Log Source Parameters section, enter the name of the log source in the Name box.
-
In the Configure Protocol Parameters section, enter the Log Source Identifier. This Identifier is the hostname/IP address from the data to be forwarded.
-
Click Finish.
What to do next: