GUID_REGISTRY_SETTING
Note: This check requires remote registry access for the remote Windows system to function properly.
This policy item is similar to REGISTRY_SETTING. Use it to check the value of a registry key as set by MDM software such as Microsoft InTune. These registry keys have associated GUIDs that relate to the policy that sets the final value.
Usage
<custom_item>
type : GUID_REGISTRY_SETTING
description : ["description"]
value_type : [value_type]
value : [value]
guid_reg_key : “HKLM\Path\to\location\of\GUID”
reg_key : “HKLM\Path\that\contains\special\{GUID}\marker”
reg_item : [item_name]
(optional) reg_ignore_hku_users : [value]
(optional) reg_include_hku_users : [value]
</custom_item>
Use field guid_reg_key to obtain the GUID value to enter in the reg_key field. The reg_key field must contain {GUID} in the location that the GUID should be found.
Example
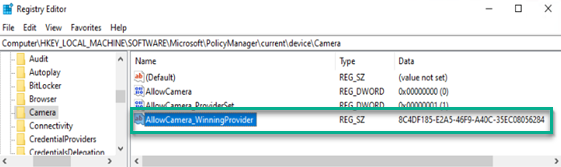
This target has AllowCamera set with an InTune policy:
The AllowCamera_WinningProvider value is set as a GUID. This path relates to the guid_reg_key tag and field value. Taking this value, the lookup is performed against the reg_key tag and field:
This example can be used in an audit file with the following values:
<custom_item>
type : GUID_REGISTRY_SETTING
description : "Disable Camera"
value_type : POLICY_DWORD
value_data : 0
reg_key : "HKLM\SOFTWARE\Microsoft\PolicyManager\Providers\{GUID}\default\Device\Camera"
reg_item : "AllowCamera"
guid_reg_key : "HKLM\SOFTWARE\Microsoft\PolicyManager\current\device\Camera"
</custom_item>
USERs and SID GUID Registry Entries
You can set policies that affect user SID registry keys. However, this deviates from normal REGISTRY_SETTING HKU checks, in that the policy is still set within the HKLM hive.
These values are substituted similar to the {GUID} values above, and uses {USER_SID} as a special marker in addition to {GUID}.
Example
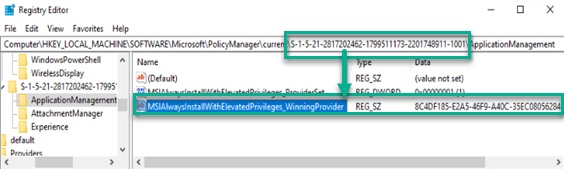
This target has MSIAlwaysInstallWithElevatedPrivileges set with an InTune policy. The policy affects a user in the S-1-5-21 range, and also sets the GUID of the winning policy:
Using both the USER SID and the GUID value, the final lookup can be performed against the actual value:
This example can be used in an audit file with the following values. Note the usage of {USER_SID} and {GUID}, which must be present for the lookups to function as intended:
<custom_item>
type : GUID_REGISTRY_SETTING
value_type : POLICY_DWORD
value_data : 0
reg_key : "HKLM\SOFTWARE\Microsoft\PolicyManager\Providers\{GUID}\default\{USER_SID}\AttachmentManager"
reg_item : "MSIAlwaysInstallWithElevatedPrivileges"
guid_reg_key : "HKLM\SOFTWARE\Microsoft\PolicyManager\current\{USER_SID}\AttachmentManager"
reg_ignore_hku_users : "S-1-5-18,S-1-5-19,S-1-5-20"
</custom_item>
You can modify the usage of reg_ignore_hku_users and reg_include_hku_users to match expected results.
value_type
The following main value_type field types are available:
-
POLICY_DWORD
-
value_data: DWORD or RANGE [same dword as in registry or range]
-
-
POLICY_TEXT
-
value_data: "TEXT" [same text as in registry]
-
-
POLICY_MULTI_TEXT
-
value_data: "TEXT1" && "TEXT2" && ... && "TEXTN" [same texts as in registry]
-