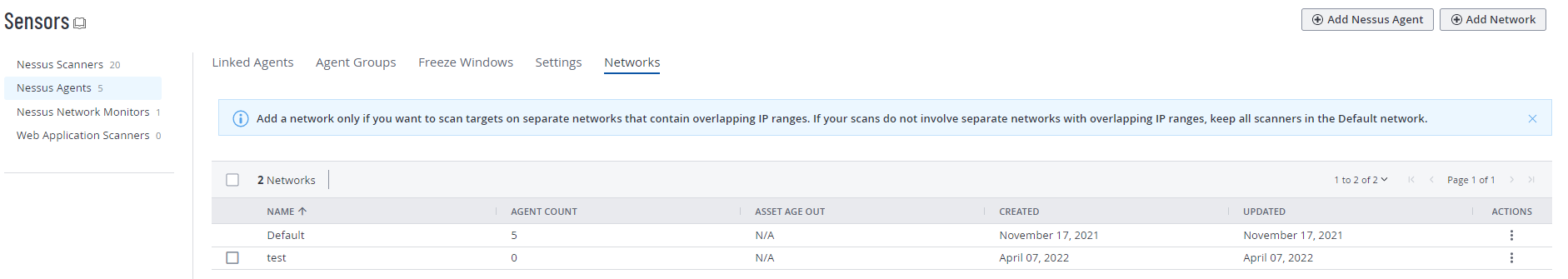
Networks
In larger enterprises, you can reduce the time and cost of setting up and maintaining locations by deploying environments with the same internal IP addresses. To disambiguate between assets that have the same IP addresses across environments, use networks in Tenable Vulnerability Management. Networks can also be used to logically separate assets for reporting, Role-Based Access Control (RBAC), and Tagging purposes.
If you deploy environments with the same internal IP addresses, create a network for each environment you have, and assign scanners and scanner groups to each network. When a scanner scans an asset, the associated network is added to the asset's details. You can filter assets by network or create dynamic tags based on a network. Recast rules and access groups do not support networks.
A scanner or scanner group can only belong to one network at a time.
There are two types of networks:
-
Default network — The network to which a scanner or scanner group belongs unless you assign it to a custom network.
You can view scanners in the default network, but you cannot add or remove scanners from the default network. If you remove a scanner or scanner group from a custom network, or if you delete a custom network, Tenable Vulnerability Management returns the scanner or scanner groups to the default network. Imported scans always belong to the default network.
Note: The following can only appear in the Default network:- Assets from AWS pre-authorized scanners
Note: If you move agents from a custom network to the Default network, you need to move the agents' associated assets to the Default network manually. Assets do not revert back to the Default network automatically. For more information, see Add an Agent to a Network and Move Assets to a Network.
-
Custom network — A custom network that you create. Custom networks allow you to group and separate different scanners and assets based on your business needs. For example, you can create networks for different sub-organizations, external versus internal scanning, or ephemeral versus static scanning.
Caution: Scanning an asset from a scanner that is not in the same network can create a duplicate asset record. If an asset is scanned by sensors in multiple networks, its network assignment will update to match the most recent scan. To avoid duplication and data inconsistency, make sure all scanners or scanner groups are assigned to the correct network. Only scan each asset using sensors from one network.
For information about managing your networks, see Manage Networks.