Remediation Summary
Unpatched assets expose organizations to vulnerabilities that can be exploited. When new assets are added to the network and scanned for the first time, any related vulnerabilities for which a patch has been available but not applied are displayed. Ideally, organizations with an effective vulnerability management process patches vulnerabilities during the initial build process.
Assets with the largest number of missing patches typically represent a higher level of remediation effort and may be the most time-consuming to address. Vulnerability severity, exploitability, and time since a patch was made available are displayed as the key points of vulnerability management. Organizations with an effective vulnerability management program will typically patch within 90 days of the date the patch is made available, and usually has lower counts in the last two rows of these matrices. These organizations will most likely only have data presented in the first row (under 30 days), especially for the highest severity vulnerabilities.
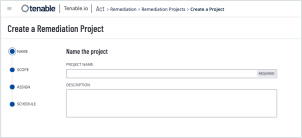
Assets that are exploitable or have a higher severity rating represent a fast lane for attackers. Prioritizing remediation of these vulnerabilities is an effective strategy to reduce risk. Tenable has provided a method to create a Remediation Project so findings can be prioritized, the scope of work can be defined, projects can be assigned, and progress can be tracked. Remediation projects can be set to be completed at a fixed date, or within a specified timeframe.
More information on the creation, viewing, editing, closing, or suspending of remediation projects can be found on the Remediation Projects page of the Tenable documentation. Remediation projects, which are created within Tenable Vulnerability Management, can also be exported as a .csv for use outside of Tenable Vulnerability Management.