Tenable One: Google Workspace IdP
One of the most common IdPs used to configure SAML with Tenable One is Google Workspace. The following steps guide you through the configuration process from start to finish, including optional configurations associated with user role and group mapping.
Manual configuration requires the following:
-
ACS URL: A custom URL provided by Tenable in the following format:
https://cloud.tenable.com/saml/login/PLACEHOLDERTip: FedRAMP environments use the following custom URL format: https://fedcloud.tenable.com/saml/login/PLACEHOLDER -
Entity ID: A custom ID provided by Tenable during SAML configuration in the following format:
TENABLE_IO_PLACEHOLDER -
A certificate within the SAML metadata object that matches the data originally sent to Tenable.
Note: Tenable does not support the use of multiple certificates and only extracts the first certificate from the metadata object. If the object includes multiple certificates, you must specify which certificate to use if it is not the first one listed.
Google Workspace: Create Initial Application Integration
To create an application in Google Workspace:
-
In your browser, sign in to the Google Admin console.
-
In the navigation menu, navigate to Apps > Web and mobile apps.
The Web and mobile apps page appears.
-
Click Add App > Add custom SAML app.
The App details pane appears.
-
In the App name text box, type a name for your application (for example, Tenable One).
-
Click Continue.
The Google Identity Provider details pane appears.
-
Skip Option 1 and Option 2 and click Continue.
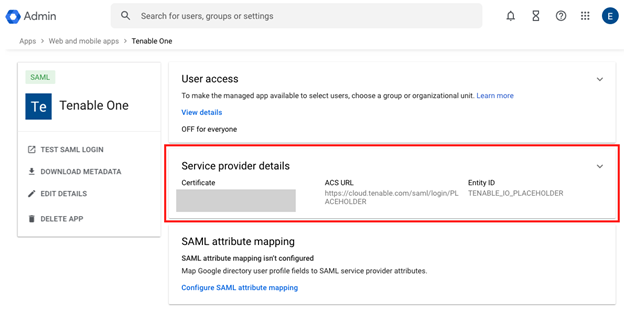
The Service provider details pane appears.
-
In the ACS URL text box, type the following placeholder URL:
https://cloud.tenable.com/saml/login/PLACEHOLDERNote: You will later replace PLACEHOLDER with a unique UUID for the SAML configuration. This link is case-sensitive. -
In the Entity ID text box, type the following placeholder text:
TENABLE_IO_PLACEHOLDERNote: You will later replace PLACEHOLDER with a unique UUID for the SAML configuration. -
Click Continue.
The Attribute mapping pane appears.
- Click Finish.
The application details appear.
-
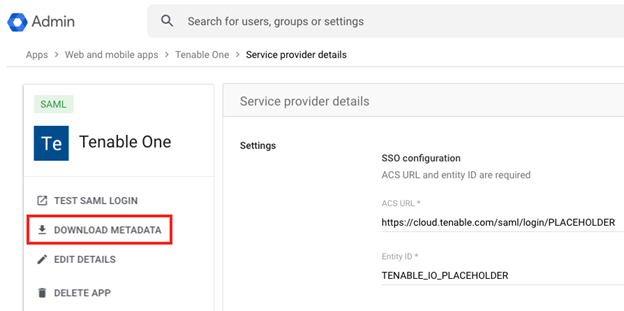
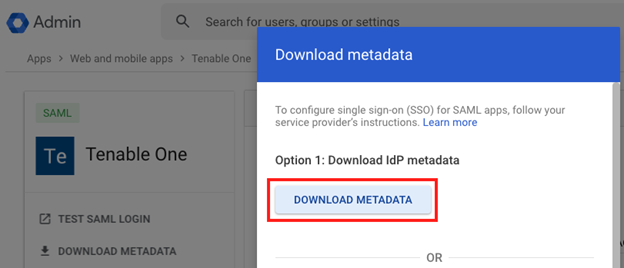
Click Download Metadata.
The Download metadata page appears.
-
Under Option 1: Download IdP metadata, click Download Metadata.
Your browser downloads the metadata.xml file.
-
Click Close.
Tenable One SAML Configuration
Once you have downloaded your medata.xml file, you can use it to configure SAML in Tenable One. You can configure this directly in the Tenable Vulnerability Management application.
To set up the Tenable One SAML configuration:
- In your browser, navigate to Tenable One.
- On the Workspace page, click Tenable Vulnerability Management.
The Tenable Vulnerability Management user interface appears.
-
In the upper-left corner, click the
 button.
button. The left navigation plane appears.
-
In the left navigation plane, click Settings.
The Settings page appears.
-
Click the SAML tile.
The SAML page appears.
-
In the action bar, click
 Create.
Create.The SAML Settings page appears.
-
Do one of the following:
 To provide configuration details by uploading the metadata.xml file from your IdP:
To provide configuration details by uploading the metadata.xml file from your IdP:
-
In the first drop-down box, select Import XML.
Note: Import XML is selected by default.
-
The Type drop-down box specifies the type of identity provider you are using. Tenable One supports SAML 2.0 (for example, Okta, OneLogin, etc.).
This option is read-only. -
Under Import, click Add File.
A file manager window appears.
-
Select the metadata.xml file.
The metadata.xml file is uploaded.
 To manually create your SAML configuration using data from the metadata.xml file from your IdP:
To manually create your SAML configuration using data from the metadata.xml file from your IdP:
-
In the first drop-down box, select Manual Entry.
A SAML configuration form appears.
-
Configure the settings described in the following table:
Settings Description Enabled toggle A toggle in the upper-right corner that indicates whether the SAML configuration is enabled or disabled.
By default, the Enable setting is set to Enabled. Click the toggle to disable SAML configuration.
Type Specifies the type of identity provider you are using. Tenable One supports SAML 2.0 (for example, Okta, OneLogin, etc.).
This option is read-only.Description A description for the SAML configuration. IdP Entity ID The unique entity ID that your IdP provides.
Note: If you want to configure multiple IdPs for a user account, create a new configuration for each identity provider with separate identity provider URLs, entity IDs, and signing certificates.
IdP URL The SAML URL for your IdP. Certificate Your IdP security certificate or certificates.
Note: Security certificates are found in a metadata.xml file that your identity provider provides. You can copy the content of the file and paste it in the Certificate box.
User Auto Provisioning Enabled A toggle that indicates whether automatic user account creation is enabled or disabled. Automatic account provisioning allows users with an account for the IdP named in the SAML configuration to create a Tenable Vulnerability Management account the first time they log in via the IdP.
Note: This option only appears during intial configuration if the setup is manual. Otherwise, you must edit the configuration after initial setup to enable this option.IdP Assigns User Role at Provisioning To assign a user role during provisioning, enable this toggle. In your SAML identity provider, add an attribute statement with userRoleUuid as the attribute name and the user role UUID as the attribute value. To obtain the UUID for a user role, go to Settings > Access Control > Roles.
Note: This option only appears during intial configuration if the setup is manual. Otherwise, you must edit the configuration after initial setup to enable this option.IdP Resets User Role at Each Login To assign a role each time a user logs in, overwriting the current role with the one chosen in your IdP, enable this toggle. In your SAML identity provider, add an attribute statement with userRoleUuid as the attribute name and the user role UUID as the attribute value.
To obtain the UUID for a user role, go to Settings > Access Control > Roles.
Note: This option only appears during intial configuration if the setup is manual. Otherwise, you must edit the configuration after initial setup to enable this option.Group Management Enabled Enable this toggle to allow the Tenable One SAML configuration to manage user groups. You must enable this toggle for the Managed by SAML option to function successfully.
-
-
Click Save.
Tenable Vulnerability Management saves your SAML configuration and you return to the SAML page.
-
Click on the SAML configuration you just created.
The SAML Settings page appears.
-
Copy both the URL and Entity ID values. You will need both of these values for the final configuration in your IdP.
Optional: Configure One or More User Groups to Automatically Add a User upon SAML Login
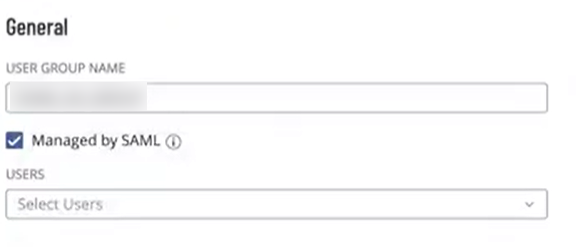
User groups allow you to manage user permissions for various resources in Tenable One. When you assign users to a group, the users inherit the permissions assigned to the group. When you enable the Managed by SAML option for a user group, Tenable One allows you to automatically add any user that logs in via SAML to that group.
Before you begin:
Ensure you've enabled the Group Management Enabled toggle when configuring the SAML settings within Tenable One.
To enable the Managed by SAML option:
-
In Tenable Vulnerability Management, in the upper-left corner, click the
 button.
button. The left navigation plane appears.
-
In the left navigation plane, click Settings.
The Settings page appears.
-
Click the Access Control tile.
The Access Control page appears.
-
Click the Groups tab.
The Groups page appears.
-
In the user groups table, click the user group to which you want to automatically add your SAML users.
The Edit User Group page appears.
-
In the General section, select the Managed by SAML check-box.
-
Click Save. Tenable Vulnerability Management saves your changes. Once you configure the related claim within your IdP, any time a user logs in via your SAML configuration, Tenable One automatically adds them to the specified user group.
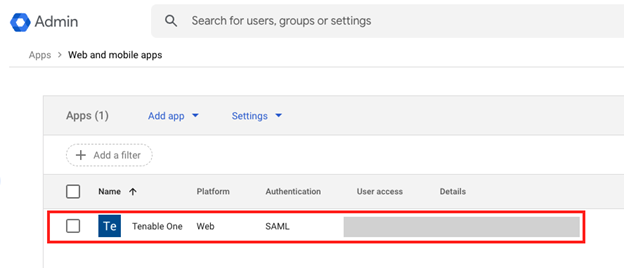
Google Workspace: Configure Final Application Integration and Upload Metadata
Now that you have completed your Tenable One SAML configurations and copied the associated URL and Entity ID values, you can update your Tenable application in Google Workspace.
-
In your browser, navigate to the Google Admin console.
-
In the navigation menu, navigate to Apps > Web and mobile apps.
The Web and mobile apps page appears.
-
Select the newly created application.
The application details appear.
- Click on the Service provider details section.
The Settings page appears.
-
In the ACS URL text box, replace the placeholder value with the previously saved URL value.
Tip: This URL is in the following format: https://cloud.tenable.com/saml/login/PLACEHOLDER. -
In the Entity ID text box, replace the placeholder value with the previously saved Entity ID value.
Tip: This ID is in the following format: TENABLE_IO_PLACEHOLDER. -
Click Save.
Google Workspace saves your changes to the permanent application, and your SAML configuration is ready for use.
Optional: Finalize Configuration for Managed by SAML Group Option
If you configured the Managed by SAML option to automatically add any user that logs in via SAML to a user group, then you must configure a related group claim within Google Workspace.
To configure the IdP group claim:
-
In your browser, navigate to the Google Admin console.
-
In the navigation menu, navigate to Apps > Web and mobile apps.
The Web and mobile apps page appears.
-
Select the newly created application.
The application details appear.
-
Click SAML attribute mapping.
The Attributes page appears.
- In the Group membership section:
In the Google groups search box, search for (and select) the appropriate Google Workspace group.
In the App attribute text box, type groups.
-
Click Save. Any time a user logs in via your SAML configuration, Tenable One automatically adds them to the specified user group in Tenable One.
Optional: Configure Managed by SAML Role Option
Roles allow you to manage privileges for major functions in Tenable One and control which Tenable One resources users can access. If you toggled on the SAML configuration options IdP Assigns User Role at Provisioning and/or IdP Resets User Role at Each Login (to automatically add and/or assign any user that logs in via SAML to a user role), then you must complete the following three steps in Google Workspace:
Add a Custom Attribute for Roles
To add a custom attribute for roles:
-
In the navigation menu, navigate to Directory > Users.
The Users page appears.
-
Click More options > Manage custom attributes.
The Manage user attributes page appears.
-
Click Add Custom Attribute.
The Add custom fields page appears.
-
In the Category text box, type a category name (e.g. Tenable).
-
In the Custom fields section:
-
In the Name text box, type a name for this attribute (e.g. User Role UUID).
-
In the Info type drop-down, select Text.
-
In the Visibility drop-down, select your preferred visibility.
-
In the No. of values drop-down, select Single Value.
-
-
Click Add.
Configure the Attribute for a User
To configure the attribute for a user (with a user role UUID):
-
On the Users page, click the name of the user for which you want to configure the attribute.
The user configuration page appears.
-
In the User Details section, click User information.
The User Details page appears.
-
Click on the recently created custom attribute.
-
In the text box, type the UUID of the Tenable user role.
Tip: Tenable user role UUIDs can be found in Tenable Vulnerability Management, in the Settings > Access Control > Roles table. -
Click Save.
Configure the Role Claim
To configure the role claim:
-
In the navigation menu, navigate to Apps > Web and mobile apps.
The Web and mobile apps page appears.
-
Select the newly created application.
The application details appear.
-
Click SAML attribute mapping.
The Attributes page appears.
- In the Google Directory attributes drop-down, select the appropriate Google Workspace custom attribute for the user role.
- In the App attributes text box, type userRoleUuid.
- Click Save.
Any time a user logs in via your SAML configuration, Tenable One automatically adds them to the specified user role.
Additional Resources
For more information on Google Workspace IdP configuration, see the following resources: