Recast
Customizing your risk management framework allows you to align scan findings with your organization's specific security posture and policies.Tenable Vulnerability Management provides three primary tools for this purpose: Recast rules adjust the CVSS-based severity of vulnerabilities and web application findings; Change Result rules manually override host audit statuses to reflect specific compliance states; and Accept rules formally acknowledge and hide risks that do not require active remediation. These rules ensure that dashboards and reports accurately reflect the current risk profile of your environment.
Rule Types
To keep your security posture accurate, use the following Rule Types:
Recast Rules—These rules allow you to manually adjust the severity of a vulnerability (for example, from Critical to Low or vice-versa). Use this to align the technical finding with your organization's internal risk assessment and remediation priorities.
Change Result Rules—Use these rules for host audits to manually mark a failed audit check to a Passed status or vice-versa. This ensures accurate reporting when you have addressed a configuration issue through a method that the standard scan cannot automatically detect.
Accept Rules—These rules hide findings for which your organization has officially accepted the risk. By removing these known exceptions from your active views, you keep your dashboards clean and focused on actionable threats.
Rule Evaluation: As new findings are imported, they are queued for evaluation against your recast rules. It is possible for a new finding to appear in the Explore > Findings view before your rule has been evaluated and applied to it.
View Caching: After a recast rule has been evaluated and the Revised Finding count is updated in the recast rules table, there is an additional cache period of up to 60 minutes for the Explore > Findings view to reflect this change.
Rule Capacity and Global Limits
Tenable Vulnerability Management enforces a total aggregate limit of 25,000 rules per container. This quota is shared across all rule types (Recast, Accept, Change Result) and findings categories (Vulnerabilities, WAS, Host Audits).
| Evaluation Criteria | Value | Counts Toward 25k Limit? |
|---|---|---|
| Rule Status | Enabled | YES |
| Disabled | YES | |
| Expires Column | Does Not Exist | YES |
| Date is in the future | YES | |
| Date is in the past |
NO |
A rule is only removed from your 25,000-rule capacity once it passes its expiration date. This means:
-
Toggling a rule to Disabled does not reclaim space. Use this for temporary testing, but consider deleting the rule if it is no longer needed.
-
Expired rules in a table do not count toward your 25,000-rule capacity. They remain visible in your table for historical reference and can be filtered.
-
Manual deletion clears space toward the capacity. If you hit the 25,000-rule limit, you must either delete rules or wait for active rules to expire.
Expires does not exist OR Expires after [Today's Date]
Accessing the Recast Page
Required User Role: Administrator
Important: Recast rules do not modify raw scan results. To maintain a reliable security record for auditing and compliance, Tenable Vulnerability Management preserves all scan data—including results from new and future scans—as a permanent, unaltered record of exactly what the scanner detected. Instead of overwriting source data, Tenable Vulnerability Management applies your recast changes dynamically within Explore dashboards, and generated reports.
To access the Recast page:
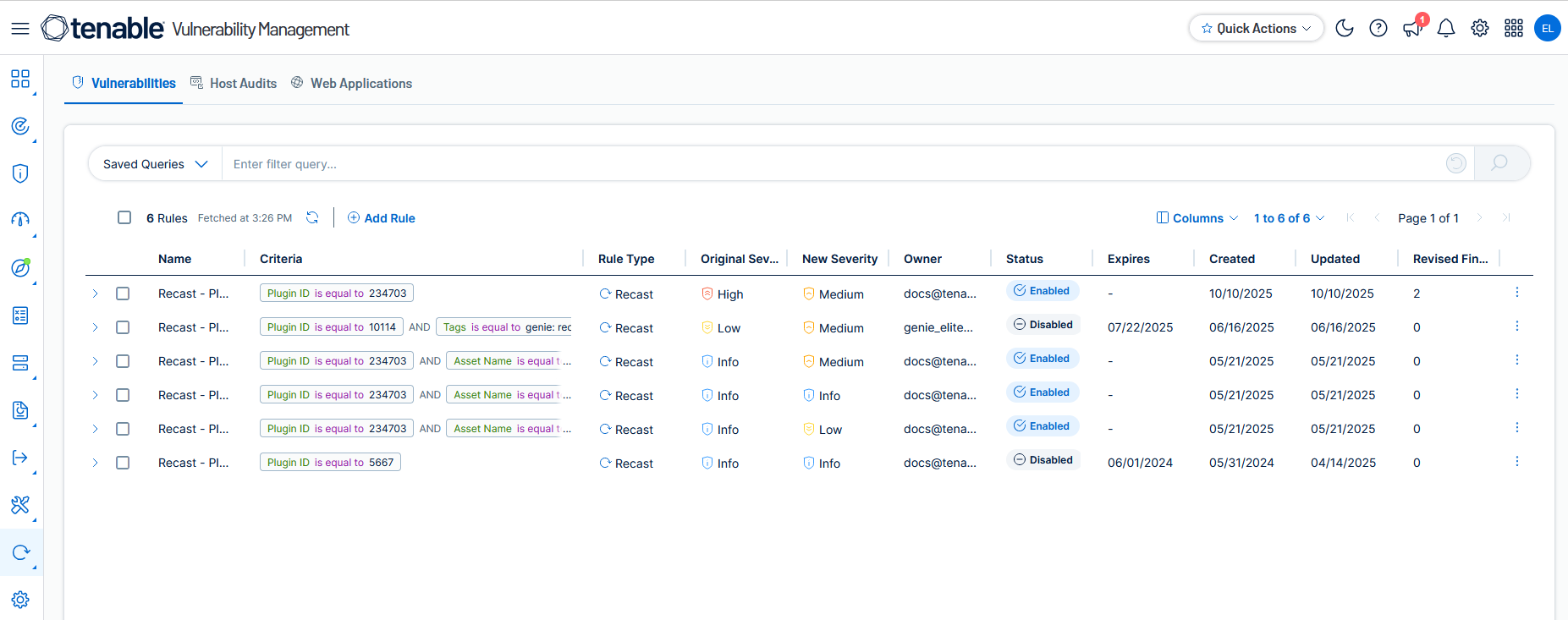
Here, you can view a table showing your current recast rules for each finding type: Vulnerabilities, Host Audits, and Web Applications.
Overview of Recast, Change Result and Accept Rules
Recast, change result and accept rules allow you to manage exceptions, but they have distinct impacts on your vulnerability metrics and reporting within Tenable Vulnerability Management. The following table compares the impact of recast, change result and accept rules.
| Feature | Recast Rule | Accept Rule | Change Result Rule |
|---|---|---|---|
| Primary Function | Changes the visible CVSS-based severity of a finding (for example, Critical to Low) to reflect an adjusted risk level. | Hides the finding from active views and moves it to a permanent or temporary accepted risk state. | Changes the status of a host audit check (for example, Failed to Passed). |
| Finding Types | Vulnerabilities and Web Applications | All | Host Audits only |
| Findings Count | Finding is still counted in your total vulnerability count, but with the new severity level. | Finding is not counted in your active vulnerability totals, dashboards, or reports by default. | Finding is moved between Failed, Passed, or Warning counts based on the rule's target result. |
| Risk Score Impact | (Requires Tenable One / Tenable Lumin license) VPR (Vulnerability Priority Rating) is not impacted and retains its original value. The change in severity, however, affects the vulnerability density count, which influences the Asset Exposure Score (AES) and Cyber Exposure Score (CES) calculation for the asset. | The VPR, AES, and CES scores of accepted findings are not altered. The underlying risk of a finding is still preserved even if it is accepted. | Does not affect VPR/AES. Improves compliance percentages for the asset. |
| Visibility | The finding remains visible on dashboards, tables, and will appear in standard reports with the modified severity label. | The finding is hidden by default across all workbenches, dashboards, and will NOT appear in standard reports (unless you specifically filter for accepted findings). | Visible in Explore tables with the updated status (for example, "Passed" or "Failed"). |
| Remediation Workflow | Re-prioritization. The finding remains in the active queue, but its new severity level adjusts its priority in remediation plans, allowing teams to either elevate or de-escalate its urgency. | Risk Acceptance. The finding is explicitly marked as an accepted business risk, signaling that no immediate remediation is planned or required. | Compliance Alignment. Marks a requirement as met (or failed) based on manual verification or organizational policy. |
| Audit Trail? | Yes. Rule history and original data are preserved within the Recast rules management page. |
Yes. Rule creation details, including mandatory justification and expiration, are stored within the rule's history. |
Yes. Manual overrides and justifications are captured and viewable within the specific rule details. |
In This Section
This documentation explains how to add recast, change result, and accept rules, what filters are available for building criteria queries, when to use them, and how to manage them. Also, you can view details about available recast columns for each finding type. For more information, see the following topics:
| Topic | Content |
|---|---|
| About Recast Rules | Learn how to recast outcomes of vulnerability and web applications findings, understand their impact on scoring, and view findings and assets that are impacted by a recast rule. |
| About Change Result Rules | Learn how to change the result of a host audit and view findings and assets that are impacted by a change result rule. |
| About Accept Rules | Learn how to accept outcomes of vulnerability and web applications findings, understand their impact on scoring, and view findings and assets that are impacted by an accept rule. |
| Recast Rule Details | Understand the details pane for each recast rule type. |
| Add Recast, Change Result, and Accept Rules | Understand how to add new recast rules for each finding type: Vulnerabilities, Host Audits, and Web Application Findings. |
| Manage Recast Rules | Learn how to manage recast rules. |
| Recast Columns | Understand the columns in the tables for each of Vulnerabilities, Host Audits, and Web Application Findings. |
| Recast Filters | Know the filters available for your criteria queries for each finding type. |