BitSight Connector
The following is not supported in Tenable FedRAMP Moderate environments. For more information, see the Tenable FedRAMP Product Offering.
The following steps allow you to configure this connector for use with Tenable Exposure Management from start to finish.
Connector Details
| Details | Description |
|---|---|
|
Supported products |
|
|
Category |
DAST |
|
Ingested data |
Assets and Findings |
|
Ingested Asset Classes |
Devices Web Applications |
|
Integration type |
UNI directional (data is transferred from the Connector to Tenable Exposure Management in one direction) |
|
Supported version and type |
SaaS (latest) |
Prerequisites and User Permissions
Before you begin configuring the connector, make sure to:
-
Create a BitSight user with the Reader permission.
-
Identify your BitSight server URL.
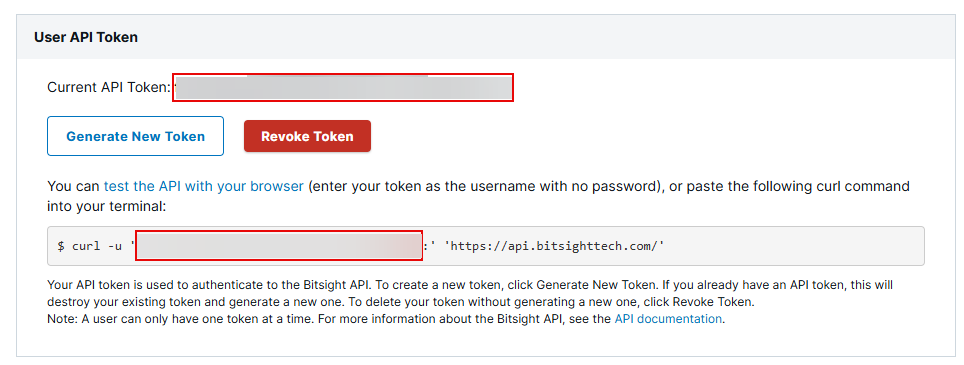
Generate BitSight API Key
-
Log in to the BitSight platform.
-
Navigate to > Settings > Account > API Token.
-
Click Generate New Token (API Key).
-
Copy the API Key to a safe location. You need it to configure the connector.
Add a Connector
To add a new connector:
-
In the left navigation menu, click Connectors.
The Connectors page appears.
-
In the upper-right corner, click
 Add new connector.
Add new connector.The Connector Library page appears.
-
In the search box, type the name of the connector.
-
On the tile for the connector, click Connect.
The connector configuration options appear.
Configure the Connector
To configure the connector:
-
(Optional) In the Connector's Name text box, type a descriptive name for the connector.
-
(Optional) To use a preconfigured on-prem connector to connect to this connector, from the Gateway drop-down, select the on-prem connector you want to use for the connector. Otherwise, select Don't use gateway.
Note: For information about configuring a gateway, see Tenable On-Prem Connector. - In the Server URL text box, paste the url of your Bitsight server.
-
In the API Key text box, paste the API key you generated in Bitsight.
-
In the Data pulling configuration section, you can configure dynamic settings specific to the connector.
-
You can configure how Tenable Exposure Management ingests company data from Bitsight. Two options are available:
-
To sync with specific company IDs: Click Load Company IDs, and then select the Bitsight company IDs you want to ingest during each sync.
-
To fetch all companies automatically: Select the Always fetch all companies check box. The connector will ingest data from all companies associated with your Bitsight account during each sync.
-
-
In the Asset Retention text box, type the number of days after which you want assets to be removed from Tenable Exposure Management. If an asset has not been detected or updated within the specified number of days, it is automatically removed from the application, ensuring your asset inventory is current and relevant.
Tip: For more information, see Asset Retention.
-
-
(Optional) To exclude vulnerabilities based on lifetime-expired risk vectors, select the Map lifetime expired risk vector vulnerabilities as Ignored check box.
-
In the Test connectivity section, click the Test Connectivity button to verify that Tenable Exposure Management can connect to your connector instance.
-
A successful connectivity test confirms that the platform can connect to the connector instance. It does not, however, guarantee that the synchronization process will succeed, as additional syncing or processing issues may arise.
-
If the connectivity test fails, an error message with details about the issue appears. Click Show tests for more information about the exact error.
-
-
In the Connector scheduling section, configure the time and day(s) on which you want connector syncs to occur.
Tip: For more information, see Connector Scheduling. -
Click Create. Tenable Exposure Management begins syncing the connector. The sync can take some time to complete.
-
To confirm the sync is complete, do the following:
-
Navigate to the Connectors page and monitor the connector's status. Sync is complete once the connector status is Connected.
-
View the sync logs for the connector to monitor the logs for a successful connection.
-
BitSight in Tenable Exposure Management
Locate Connector Assets in Tenable Exposure Management
As the connector discovers assets, Tenable Exposure Management ingests those devices for reporting.
To view assets by connector:
-
In Tenable Exposure Management, navigate to the Assets page.
-
In the Filters section, under 3rd Party Connectors, click the connector name for which you want to view assets.
The asset list updates to show only assets from the selected connector.
-
Click on any asset to view Asset Details.
Locate Connector Weaknesses in Tenable Exposure Management
As the connector discovers weaknesses, Tenable Exposure Management ingests those weaknesses for reporting.
To view weaknesses by connector:
-
In Tenable Exposure Management, navigate to the Weaknesses page.
-
In the Filters section, under 3rd Party Connectors, click the connector name for which you want to view weaknesses.
The weaknesses list updates to show only weaknesses from the selected connector.
-
Click on any weakness to view Weakness Details.
Locate Connector Findings in Tenable Exposure Management
As the connector discovers individual findings, Tenable Exposure Management ingests those findings for reporting.
To view findings by connector:
-
In Tenable Exposure Management, navigate to the Findings page.
-
In the Filters section, under 3rd Party Connectors, click the connector name for which you want to view findings
The findings list updates to show only assets from the selected connector.
-
Click on any asset to view Finding Details.
Data Mapping
Exposure Management integrates with the connector via API to retrieve relevant weakness and asset data, which is then mapped into the Exposure Management system. The following tables outline how fields and their values are mapped from the connector to Exposure Management.
Device Mapping
| Tenable Exposure Management UI Field |
BitSight Field |
|---|---|
| Unique Identifier | asset |
| Asset - Name | asset |
| Asset - Operating Systems |
products.product (if type = operating system) |
|
Asset - IPv4 Adresses Asset - IPv6 Adresses |
ip_addresses |
|
Asset - External Tags |
tags |
| Asset Custom Attributes |
products.version |
Device Finding Mapping
| Tenable Exposure Management UI Field |
BitSight Field |
|---|---|
| Unique Identifier | evidence_key |
| Finding Name | help_text/message |
| Severity Driver | severity |
| Description | help_text |
| Port | dest_port |
| First Seen | first_seen |
| Last seen (Observed) | last_seen |
| Finding Custom Attributes |
temporary_id evidence_key remaining_decay grade impacts_risk_vector_details risk_vector_label risk_category severity_category |
Web Application Mapping
| Tenable Exposure Management Value |
BitSight Field |
|---|---|
| Unique Identifier | asset |
| Asset - Name | asset |
| Asset - Webapp Homepage Screenshot Url | asset
(if asset_type = Domain) |
|
Asset - External Tags |
tags |
Web Application Finding Mapping
| Tenable Exposure Management UI Field |
BitSight Field |
|---|---|
| Unique Identifier | evidence_key |
| Finding Name | help_text/message |
| Severity Driver | severity |
| Description | help_text |
| First Seen | first_seen |
| Last seen (Observed) | last_seen |
| Finding Custom Attributes |
temporary_id evidence_key remaining_decay grade impacts_risk_vector_details risk_vector_label risk_category severity_category |
Finding Status Mapping
|
Tenable Exposure Management Status |
BitSight Status |
|---|---|
|
Active |
All other statuses, including: lifetime_expired_ignored=True impacts_risk_vector_details=lifetime_expired risk accepted |
|
Fixed |
resolved remaining_decay=0 |
Note:For BitSight, Tenable Exposure Management bases the finding status on the last_remediation_status_label field.
Finding Severity Mapping
|
Tenable Exposure Management Severity |
BitSight Score |
|---|---|
|
Critical |
9-10 |
|
High |
7-8 |
|
Medium |
4-6 |
|
Low |
1-3 |
Note:For BitSight, Tenable Exposure Management bases the finding score on the severity field.
Status Update Mechanisms
Every day, Tenable Exposure Management syncs with the vendor's platform to receive updates on existing findings and assets and to retrieve new ones (if any were added).
The table below describes how the status update mechanism works in the connector for findings and assets ingested into Tenable Exposure Management.
|
Update Type in Tenable Exposure Management |
Mechanism (When?) |
|---|---|
|
Archiving Assets |
|
|
Change a Finding status from "Active" to "Fixed" |
|
Uniqueness Criteria
Tenable Exposure Management uses defined uniqueness criteria to determine whether an ingested asset or finding should be recognized as a distinct record. These criteria help define how assets and findings are identified and counted from each connector.
Tip: Read all about Third-Party Data Deduplication in Tenable Exposure Management .
The uniqueness criteria for this connector are as follows:
|
Data |
Uniqueness Criteria |
|---|---|
|
Asset |
asset |
|
Detection |
help_text/message |
|
Finding |
evidence_key |
| Solution | remediation_tip |
API Endpoints in Use
API version: v2
|
API |
Use in Tenable Exposure Management |
Required Permissions |
|---|---|---|
|
/ratings/v1/companies |
Get companies Ids |
Reader |
| /ratings/v1/companies/{{ company_guid }}/assets |
Assets |
Reader |
|
/ratings/v1/companies"/{{ company_guid }}/findings |
Findings |
Reader |
Data Validation
This section shows how to validate and compare data between Tenable Exposure Management and the BitSight platform.
Asset Data Validation
Objective: Ensure that the number of assets in BitSight aligns with the number of assets displayed in Tenable Exposure Management.
In BitSight:
-
Navigate to the Findings page.
-
Click on a finding to open its Details tab.
-
Review the Asset field:
-
If an asset is listed, this is the asset that will appear in Tenable Exposure Management.
-
If no asset is listed, the finding is considered assetless and will not appear in Tenable Exposure Management.
-
In Tenable Exposure Management:
-
Compare the total number of assets between BitSight and Tenable Exposure Management.
Expected outcome: Only findings that are tied to an asset in BitSight will be represented as assets in Tenable Exposure Management. Asset counts may differ if BitSight findings are not associated with an asset.
If an asset is not visible in Exposure Management, check the following conditions:
-
The asset was archived based on its last observed date (last_seen field).
-
The asset was archived because it did not return in the connector's last sync.
Tip: To learn more on how assets are archived and findings change status, see Status Update Mechanisms.
Finding Data Validation
Objective: Ensure that the number of findings in BitSight aligns with the number of findings in Tenable Exposure Management.
In BitSight:
-
Navigate to the Findings page.
-
Each finding includes a Risk Vector, Finding Identifier, and Details.
-
These parameters are used to determine uniqueness. Each unique finding should be reflected in Tenable Exposure Management.
-
In Tenable Exposure Management:
-
Compare the total number of findings between BitSight and Tenable Exposure Management.
Findings are considered unique based on the combination of:
-
Risk Vector
-
Finding Identifier
-
Details (mapped from BitSight remediation name)
-
Expected outcome:Tenable Exposure Management may display fewer findings if multiple BitSight entries share the same unique combination, or if findings are not tied to an asset.
If a finding is missing from Exposure Management or no longer active, check the following conditions:
-
The finding is marked as Fixed and appears under the Fixed state on the Findings screen.
-
The finding no longer appears because its related asset was archived.
Tip: To learn more on how assets are archived and findings change status, see Status Update Mechanisms.